Structure of InfoSec
In this module, our goal is to provide you with a foundational understanding of information security: how it is structured, which roles are assumed by whom, the various domains/areas of expertise within cybersecurity, and what career opportunities are currently available. This module is fundamentally designed for complete newcomers, those who have found the motivation and made the decision to take the plunge into the vast ocean of cybersecurity.
To make the dive less daunting, we'll give you the necessary overview of how Information Security is broadly structured and organized. The goal here is to equip you with enough knowledge to help you decide where you want to swim, and to develop a sense of the direction you need to take.
Author's side note:
Since we assume you are "new" to this field, unfortunately, we won't be able to hand you practical exercises right away. Imagine you're sitting in a fighter jet, eager to take off. Without knowing what anything in the cockpit is or what it's for, you'll find it extremely challenging (and time consuming) to simply start the aircraft, let alone get the fighter jet airborne. Therefore, this module is purely "theoretical", while at the same time concise and packed with all the essential details. You will encounter and discover all further aspects along your journey in the future modules. Our goal is to help you to become a great and professional specialist in the field you desire. Therefore, we have to give you the necessary picture of the Information Security world first.
Nowadays, we heavily rely on digital platforms for almost everything; communicating with friends, banking, shopping, and running businesses. This means keeping our data safe from unauthorized access or damage is crucial. Information Security, often called InfoSec, is all about safeguarding information and systems from people who must not have access to them. This includes preventing unauthorized viewing, changing, or destroying of data.
Look closely at the following graphic and try to memorize it. It illustrates, in a very simplified manner, the approximate structure/landscape of the digital world. We will go through this piece by piece in the upcoming sections, and you will understand how all these elements are interconnected.
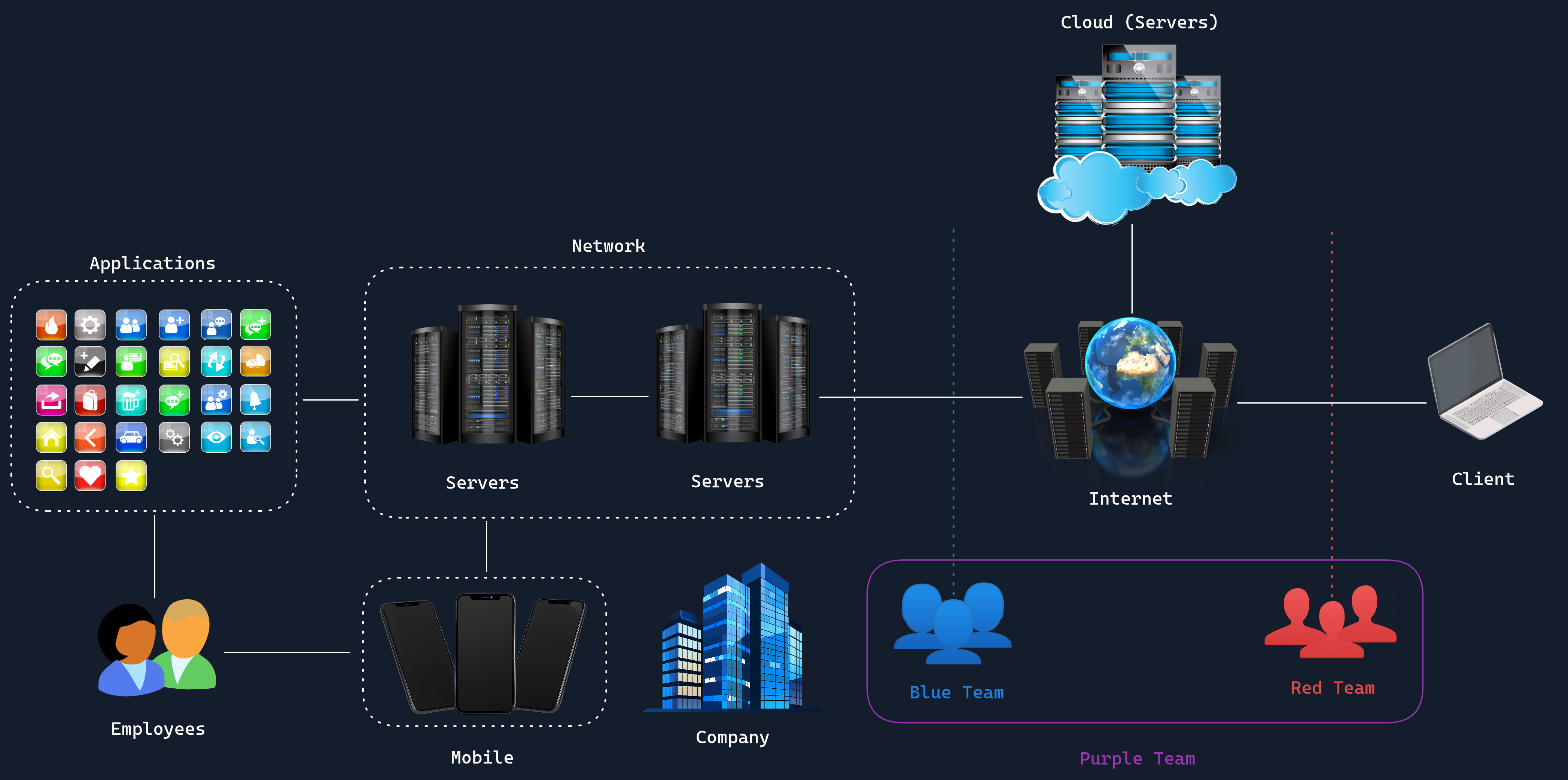
- Client: This is a PC/Laptop through which you access resources and services "on the Internet".
- Internet: This is a vast, interconnected network of servers that offer different services and applications, such as Hack The Box.
- Servers: Servers provide various services and applications designed to perform specific tasks. For example, one type of server might be a "web server", allowing you and others to view the content of a website (such as this section you're reading currently) on your computer or smartphone.
- Network: When multiple servers or computers are connected and can communicate with each other, it's called a network.
- Cloud: Cloud refers to data centers that offer interconnected servers for companies and individuals to use.
- Blue Team: This team is responsible for the internal security of the company and defends against cyber attacks.
- Red Team: This team simulates an actual adversary/attack on the company.
- Purple Team: This team consists of both Blue Team and Red Team members working together to enhance the company's security.
We'll delve more into these teams and other aspects in individual sections.
If you're looking to become a penetration tester - a professional who finds and fixes security weaknesses in systems - understanding InfoSec is essential. Your job is to identify potential vulnerabilities before malicious hackers can exploit them. By learning about strong security measures, you can help organizations protect their valuable information and prevent unauthorized access.
More services and systems are moving online in a trend known as digital transformation. While this shift offers many benefits like convenience and efficiency, it also creates more opportunities for cyber attacks. Hackers are getting smarter and more aggressive, aiming to steal sensitive data or disrupt services. These cyber attacks can lead to significant financial losses and damage a company's reputation and customer trust.
Imagine your information is like treasure stored in a castle. The castle's walls, drawbridges, and guards are the security measures protecting your treasure from thieves.
- The Treasure: Your valuable data and information.
- The Castle Walls: Firewalls, defensive mechanisms, and encryption that keep outsiders from getting in.
- The Guards: Security protocols and access controls that monitor who enters and leaves.
- Penetration Testers: Knights who test the castle's defenses by simulating attacks to find weak spots.
- Digital Transformation: Expanding the castle to store more treasure, which attracts more thieves.
- Cyber Threats: Thieves who are constantly looking for ways to breach the castle's defenses.
Just as a castle must strengthen its defenses as it grows and becomes a more valuable target, businesses must enhance their InfoSec measures as they move more services online. By thinking of InfoSec as a building or fortress to protect, it becomes easier to understand the importance of strong security in the digital age.
The necessity of InfoSec stems from the value of information in the digital age. Personal data, intellectual property, financial information, and government secrets are just a few examples of the critical data that needs protection. A breach can lead to severe consequences, including financial loss, reputational damage, legal ramifications, and national security threats.
Areas of Information Security
InfoSec plays an integral role in safeguarding an organization's data from various threats, ensuring the confidentiality, integrity, and availability of data. This wide-ranging field incorporates a variety of domains, and the list provided here captures some of the most general assets. However, it is essential to note that these examples merely scratch the surface of the broad spectrum that InfoSec covers.
The actual range of assets that fall under the umbrella of InfoSec is far more extensive and continues to evolve in tandem with advancements in technology and the ever-changing landscape of cyber threats, consisting of but not limited to:
- Network Security
- Application Security
- Operational Security
- Disaster Recovery and Business Continuity
- Cloud Security
- Physical Security
- Mobile Security
- Internet of Things (IoT) Security
Later on, we will also explore some of the most prevalent cyber threats, such as Distributed Denial of Service (DDoS) attacks, ransomware, advanced persistent threats (APTs), and insider threats. Additionally, we will examine the structure and function of cybersecurity teams, gaining an understanding of their areas of specialization and the key roles within these teams. This comprehensive overview will provide valuable insights into how cybersecurity professionals collaborate to mitigate and respond to these evolving threats.
Security Concepts
A risk in the context of information security refers to the potential for a malicious event to occur, which could cause damage to an organization's assets, such as its data or infrastructure. This potential for damage is typically quantified in terms of its likelihood and the severity of its impact. Risk is a broader concept that encapsulates both threats and vulnerabilities, and managing risk involves identifying and applying appropriate measures to mitigate threats and minimize vulnerabilities.
A threat, on the other hand, is a potential cause of an incident that could result in harm to a system or organization. It could be a person, like a cybercriminal or hacker, or it could be a natural event, like a fire or flood. Threats exploit vulnerabilities to compromise the security of a system.
A vulnerability is a weakness in a system that could be exploited by a threat. Vulnerabilities can exist in various forms, such as software bugs, misconfigurations, or weak passwords. The presence of a vulnerability doesn't necessarily mean a system will be compromised; there must also be a threat capable of exploiting that vulnerability, and the potential damage that could result constitutes the risk.
In essence, a risk represents the potential for damage, a threat is what can cause that damage, and a vulnerability is the weakness that allows the threat to cause damage. All three concepts are interconnected, and understanding the difference between them is essential for effective information security management.
Roles in Information Security
In the expansive world of Information Security (InfoSec), there are a plethora of different roles each carrying their unique set of responsibilities. These roles are integral parts of a robust InfoSec infrastructure, contributing to the secure operations of an organization:
Principles of Information Security
InfoSec operates under a set of fundamental guiding principles. These principles form the bedrock and offer a comprehensive framework for the effective management, protection, and secure handling of critical and sensitive information and data assets. They provide the rules and guidelines that help to shape the policies, control measures, and practices adopted by organizations to safeguard their informational resources.
These principles are not only relevant to InfoSec professionals, but also to any individual or entity interacting with information systems. They influence everything from the design and development of secure systems, to operational practices, incident response strategies, and even the legal and ethical standards that govern the use of information technology.
Understanding these principles is crucial for anyone venturing into the field of InfoSec, as they provide the theoretical underpinnings that inform practical action. They enable professionals to make informed decisions about how to best protect information assets, and provide a clear structure for assessing the effectiveness of current security measures.
In the subsequent sections of this module, we will delve deeper into each of these principles; exploring their significance, how they are implemented in real-world scenarios, and their relevance to various InfoSec roles and responsibilities.
- Confidentiality
- Integrity
- Availability
- Non-repudiation
- Authentication
- Privacy
Processes in Information Security
InfoSec involves a set of processes designed to protect an organization’s data and information systems from unauthorized access, misuse, disclosure, destruction, and disruption. These processes form the backbone of a robust security strategy, ensuring that confidentiality, integrity, and availability (the CIA Triad) of data are maintained. The key processes in information security are as follows:
- Risk Assessment
- Security Planning
- Implementation of Security Controls
- Monitoring and Detection
- Incident Response
- Disaster Recovery
- Continuous Improvement
Purpose of Information Security
The primary purposes of InfoSec include:
- Protecting sensitive data from unauthorized access
- Ensuring business continuity
- Maintaining regulatory compliance
- Preserving brand reputation
- Safeguarding intellectual property
- Enabling secure digital transformation
Tools in Information Security
InfoSec professionals use a wide array of tools to perform their duties. As a beginner in penetration testing, you should be aware of these common categories:
- Firewalls: Control incoming and outgoing network traffic
- Intrusion Detection/Prevention Systems (IDS/IPS): Monitor for and block suspicious activities
- Security Information and Event Management (SIEM) systems: Collect and analyze security event data
- Vulnerability scanners: Identify potential weaknesses in systems and applications
- Penetration testing tools: Simulate attacks to find vulnerabilities (e.g., Metasploit, Burp Suite)
- Encryption tools: Protect data confidentiality and integrity
- Access control systems: Manage user permissions and authentication
- Security awareness training platforms: Educate users about security best practices
For penetration testing specifically, you'll need to become familiar with many tools and operating systems including but not limited to:
- Linux, Windows, MacOS
- Nmap: Network scanning and discovery
- Wireshark: Network protocol analysis
- Metasploit: Exploitation framework
- Burp Suite: Web application security testing
- John the Ripper: Password cracking
Note: As a penetration tester, you'll be using many of these tools to simulate attacks and identify vulnerabilities. However, it's crucial to understand the ethical and legal implications of using these tools. Always ensure you have proper authorization before conducting any security tests.
Understanding the structure of InfoSec provides a crucial foundation for your journey into penetration testing. It helps you understand the context of your work, the systems you'll be testing, and the broader security landscape. As you progress, you'll dive deeper into each of these areas, developing the skills needed to effectively identify and help remediate security vulnerabilities.