Operational Security, often abbreviated as OpSec, is a crucial component of an organization's overall security strategy. It encompasses the processes, practices, and decisions related to handling and protecting data assets throughout their lifecycle. The primary goal of Operational Security is to maintain a secure environment for an organization's day-to-day operations, ensuring that sensitive information remains confidential, intact, and available only to authorized individuals.
Imagine you're planning a big birthday party at your house. You have precious items, like your favorite video game console, a family heirloom, or a special piece of jewelry, that you don't want to get lost or damaged during the event. OpSec is like the plan you put in place to keep these valuables safe while still enjoying the party. Let's break down the entire process of Opsec:
1. Assets Identification
First, you figure out which items are most important to protect. These are your "critical information assets." Just as you decide that your heirloom necklace needs special care, organizations identify sensitive data that requires extra protection.
2. Threat Identification
You think about what could go wrong. Could someone accidentally knock over your gaming console? Might a guest wander into your room and misplace your jewelry? This is like analyzing threats and assessing vulnerabilities in OpSec—figuring out where things could go awry.
3. Vulnerability Identification
To prevent these issues, you take action. You might lock your valuable items in a safe place, restrict certain areas of your house, or keep an eye on guests who get too close to your prized possessions. Similarly, OpSec involves implementing measures like passwords, security badges, or surveillance cameras to protect important information.
4. Access Control
Access control is another big part of this. You decide who gets to enter your room or handle your special items. Maybe only your best friend gets the key to your room because you trust them. In the same way, companies use OpSec to determine who can access sensitive data, ensuring only the right people have the necessary permissions.
5. Monitoring
During the party, you stay alert. If you see that guests are entering areas they shouldn't, you adjust your plan—maybe you close doors or ask them politely to stay in the common areas. OpSec is just like that; it's a continuous process that adapts to new threats and changes to keep everything secure.
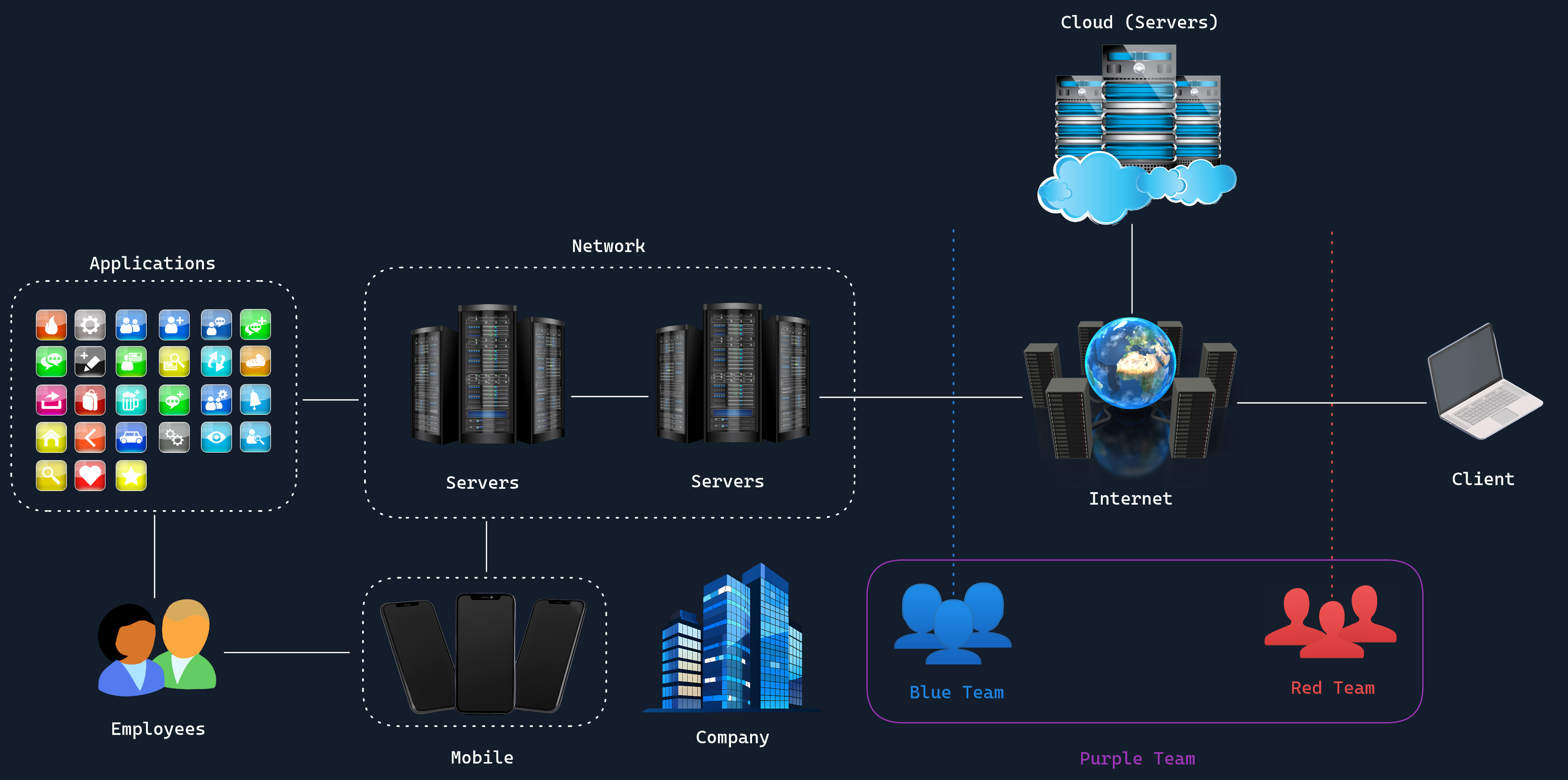
At its core, OpSec is about identifying critical information, analyzing threats, assessing vulnerabilities, and implementing appropriate protective measures. This process is continuous and dynamic, adapting to new threats and changes in the organization's operational environment. It also covers a wide range of activities, from physical security measures like controlling access to facilities, to digital practices such as implementing robust password policies and managing user permissions.
As we mentioned earlier, one of the key aspects of OpSec is access control. This involves determining who should have access to what information and systems, and under what circumstances. It includes the implementation of authentication mechanisms, such as multi-factor authentication, to verify users' identities, as well as authorization systems to ensure users can only access the resources they need for their roles. Regular audits of access rights are also a crucial part, ensuring that permissions are revoked when no longer needed, such as when an employee changes roles or leaves the organization.
Another important component is asset management, specifically the maintaining an up-to-date inventory of all information assets, including hardware, software, and data. Understanding what assets exist, where they are located, and their importance to the organization is crucial for implementing appropriate security measures. It also helps in identifying and prioritizing vulnerabilities that need to be addressed.
Change management is also a significant part of OpSec. Organizations frequently need to implement changes to their systems and processes. With OpSec you ensure that these changes are made in a controlled manner, with proper testing and approval processes in place. This helps prevent unintended security vulnerabilities from being introduced during updates or modifications to systems.
Finally, this brings us to security awareness training, a crucial aspect in ensuring that all employees understand their role in maintaining the security of their organization. This includes educating staff about phishing attacks, the importance of strong passwords, and the proper handling of sensitive information.
OpSec Responsibility
The responsibility for OpSec typically falls on the Information Security team, led by the Chief Information Security Officer (CISO), who works closely with other departments such as IT, HR, and Legal to ensure that security measures are aligned with business needs and regulatory requirements, or an equivalent role. However, it's important to note that OpSec is not solely the domain of the security team. It requires cooperation and commitment from all levels of the organization, from front-line employees to top-level executives.
Testing of Operational Security measures is often carried out by internal security teams or external consultants specializing in penetration testing and security assessments. These tests help identify weaknesses in the organization's security posture, allowing for improvements to be made before real attackers can exploit vulnerabilities. Penetration testers may attempt to bypass access controls, exploit misconfigurations, or use social engineering tactics to test the effectiveness of OpSec measures.