A Red Team is a specialized group of cybersecurity professionals who simulate real-world attacks on an organization's systems, networks, and even its people. Their goal is to test the organization's defenses comprehensively. Unlike standard security tests that might only look for technical flaws, Red Teams take a holistic approach. They examine not just the technology but also the human and physical aspects of security.
Imagine a castle that needs to be protected from invaders. The castle has high walls, a moat, guards at the gates, and watchtowers to spot approaching enemies. The king wants to ensure that the castle is truly secure, so he hires a group of experts to test its defenses. This group dresses up like enemies, tries to find hidden paths, and even attempts to trick the guards to gain entry. Their mission isn't to harm the castle but to find weaknesses so they can be fixed before real enemies exploit them. In the world of cybersecurity, this group is known as a Red Team.
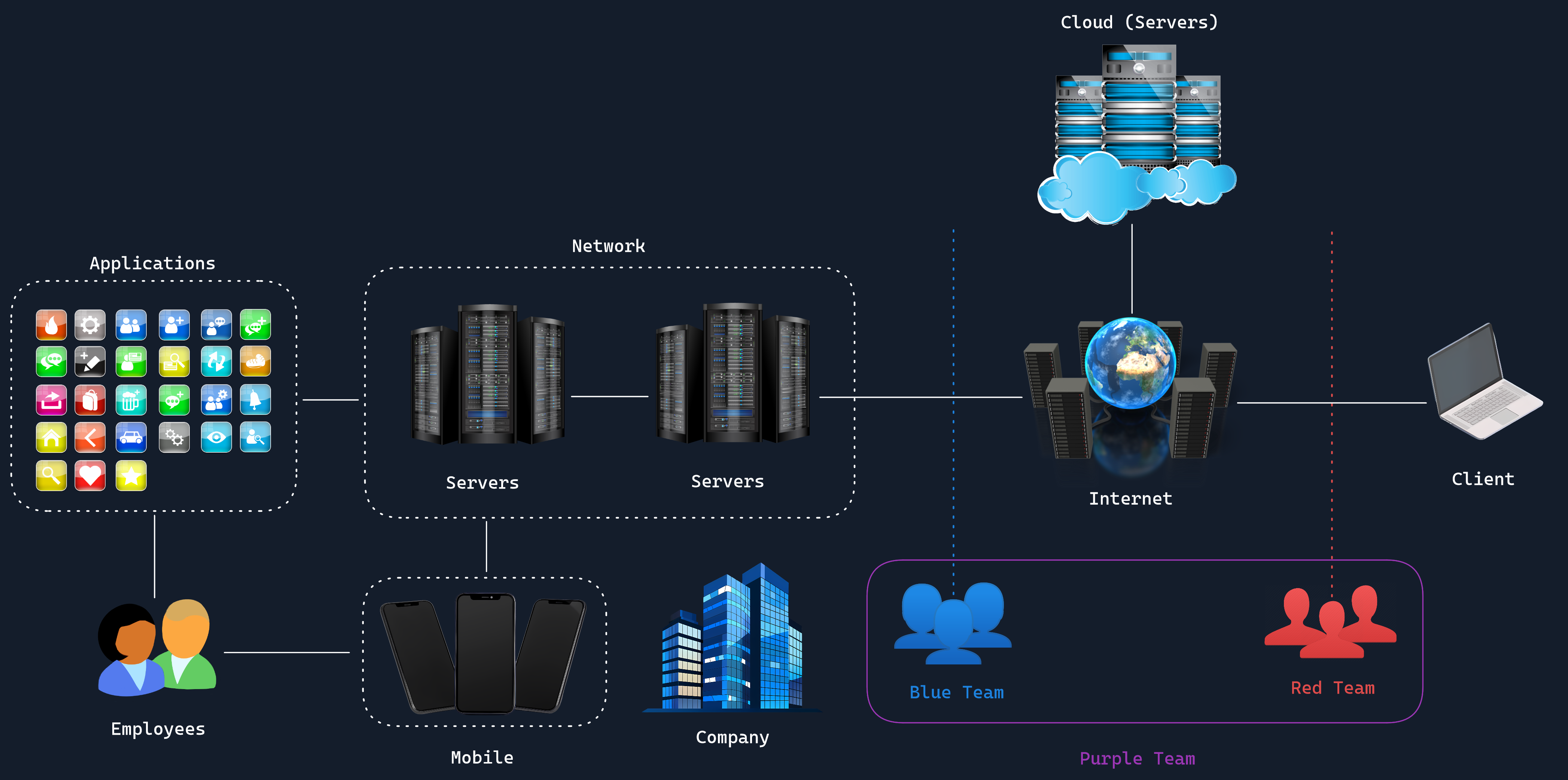
A typical Red Team is made up of experts with diverse skills, each bringing something unique to the table. Some members specialize in hacking into computer systems, finding loopholes in software or networks. Others are adept at social engineering, which means they know how to trick people into revealing confidential information, like pretending to be a trusted colleague to obtain passwords. There are also physical security experts who might try to enter secure buildings without authorization. This mix of talents allows the Red Team to attack the organization from multiple angles, just like a real-world attacker would.
For example, one team member might focus on sending convincing phishing emails to employees, hoping someone will click on a malicious link. Another might try to find an unlocked door or persuade a security guard to let them into a restricted area. By coordinating these efforts, the Red Team can uncover complex vulnerabilities that involve both technology and human behavior.
Purpose
The primary purpose of a Red Team is to improve an organization's security by identifying weaknesses that regular checks might miss. By acting like real attackers, they provide a realistic assessment of how well the organization can detect, respond to, and stop sophisticated attacks. They aim to answer questions like: Can someone break into our systems? How quickly can we detect an intrusion? Are our employees susceptible to manipulation? Their ultimate objective is to strengthen the organization's defenses against genuine threats.
Red Team engagements are usually long-term projects, lasting weeks or even months. During this time, the team carefully plans and executes their simulated attacks. They start by gathering information about the organization, much like spies gathering intelligence. They study the company's websites, employee profiles, and any publicly available information to understand potential entry points.
Once they have a plan, they begin attempting to breach the organization's defenses. This could involve hacking into networks, exploiting software bugs, or deceiving employees. The Red Team operates covertly, meaning most people in the organization are unaware of the ongoing test. This secrecy ensures that the responses they observe are genuine and not influenced by prior knowledge of the test.
Throughout the operation, the Red Team meticulously documents their activities, noting what worked, what didn't, and why. This detailed record is crucial for analyzing the organization's strengths and weaknesses.
At the end of their engagement, the Red Team produces a comprehensive report detailing their findings. This report includes how they managed to infiltrate systems, what data they could access, and recommendations for strengthening defenses. The report is typically presented to senior leadership, such as the Chief Information Security Officer (CISO), to ensure that necessary changes are implemented.
The insights provided by the Red Team are invaluable. They help the organization make informed decisions about where to invest in security measures, whether that means additional employee training, upgrading technology, or improving physical security protocols.
Objectives
Red Teams play a crucial role in enhancing an organization's cybersecurity posture through a comprehensive set of objectives. A significant focus is placed on assessing human factors, examining how susceptible employees are to social engineering tactics and phishing attempts, which often serve as entry points for cyberattacks.
Physical security is not overlooked, as Red Teams evaluate access controls, surveillance systems, and other on-site security measures. They challenge existing assumptions about security controls and policies, ensuring that what's believed to be secure actually stands up to scrutiny. By providing realistic attack scenarios, Red Teams prepare organizations for sophisticated, multi-vector threats that mirror real-world tactics used by advanced adversaries. This approach helps to improve incident response procedures, enabling organizations to react more effectively when faced with actual security incidents.
Additionally, Red Teams assess the organization's security awareness and training programs, identifying areas where employee education can be enhanced. They evaluate the effectiveness of security policies and procedures, ensuring they are practical and enforceable. Red Teams also examine the organization's supply chain security, identifying potential vulnerabilities introduced by third-party vendors or partners. By analyzing the organization's digital footprint and online presence, they help mitigate risks associated with information leakage and social media exposure. Ultimately, the insights gathered from these comprehensive assessments guide decision-making on security investments, ensuring resources are allocated where they will have the most significant impact in building a robust and resilient security posture capable of withstanding evolving cyber threats.